[German]Last Wednesday, Microsoft announced the backport of Microsoft Defender ATP automation and cloud app detection on older Windows 10 versions.
[German]Last Wednesday, Microsoft announced the backport of Microsoft Defender ATP automation and cloud app detection on older Windows 10 versions.
Advertising
General information and review
Microsoft is expanding Windows Defender to protect against threats to corporate environments. Windows Defender Advanced Thread Protection (Windows Defender ATP) provides an advanced (paid) protection solution for Windows 10 in enterprise environments. In February 2019, it became known that Microsoft had ported Windows Defender ATP to Windows 7 SP1 and Windows 8.1 (see Windows Defender ATP EDR for Windows 7/8.1 available).
Windows Defender Advanced Thread Protection (ATP) has renamed into Microsoft Defender ATP, a comprehensive protection solution for Windows 10 and macOS in enterprise environments (see Windows Defender ATP is now Microsoft Defender ATP).
(Source: YouTube)
Backport for older Windows 10 versions
Last Wednesday (June 26, 2019) Heike Ritter pointed out in a tech community article that Microsoft Defender ATP automation and cloud app detection are now also available on older Windows 10 machines.
We are pleased to announce that we've backported key Microsoft Defender ATP capabilities to earlier versions of Windows 10 so you can have the time you need to stay secure while testing and implementing updates https://t.co/DkPukRpxUt
— Microsoft Defender ATP (@WindowsATP) 26. Juni 2019
Advertising
I became aware of it through the above tweet, but first had to research what was new about it. Because I still had the blog posts mentioned above in mind.
What is the article about?
Microsoft Defender ATP automation uses state-of-the-art AI technology to resolve incidents by automatically scanning alerts, applying AIs to determine if a threat is real, and determining what action to take – from alerting to resolution in minutes. However, this automation was limited to the latest version of Windows 10.
Microsoft writes that 'many' enterprise customers on the semi-annual channel (SAC) are taking the feature updates to the latest version of Windows 10 twice a year. But Microsoft also had to learn that the rest of the total – 'many' – was significant – because these customers don't switch to the latest version of Windows 10 with all its bugs every 6 months.
From this group of corporate customers came the feedback that more time and flexibility was needed to plan, test and provide updates. Microsoft has responded by making changes to the Windows service and support lifecycle. The next step that was announced: Redmond is making the latest Microsoft Defender ATP features available for older versions of Windows 10.
Which Windows 10 versions get the backport?
One of the biggest requirements was to provide Microsoft Defender ATP automation for earlier Windows 10 versions. It was designed to help security teams on these versions to automatically scan and fix threats on their network.
Automation is now available with Windows 10, version 1709 and later. This service also includes automated investigation and remediation of memory-based (file-free) attacks. This means that the system can use automated storage forensics to load malicious storage areas and perform necessary in-memory cleanup actions.
What an administrator need to do?
To benefit from these backported functions, all you have to do is install a Windows Update. For Windows 10 Fall Creators Update (version 1709), you must install KB4493441 or later, and for Windows 10 Spring 2018 Update (version 1803), it is KB4493464 or later. Once this is done, security teams can benefit from these features on these machines.
Explanation of the terms
One of the big problems with all this stuff is that Microsoft Marketing is making up more and more sounding names. Therefore I have extracted some information below.
Microsoft Defender ATP Automation
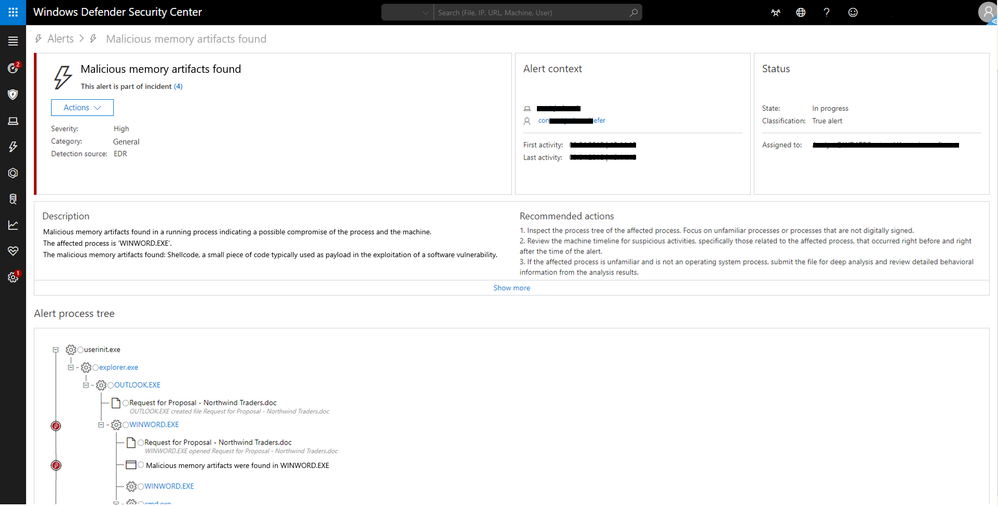
Microsoft Defender ATP service provides features to display security incidents on systems in a dashboard. As I pointed out in the above articles, these are displayed in the Windows Defender Security Center along with data from other endpoints. This gave security teams a single place to get an overview of security incidents. The data can be used to investigate and respond to incidents across the Windows environment.
The problem is that the Microsoft Defender ATP service offers a wide range of transparency regarding security incidents on the monitored computers (endpoints). But the service generates a variety of alerts, the amount of which can be challenging for a typical security operations team, as Microsoft says here.
After Microsoft gained this insight, they began to to develop some automation. To meet this challenge, Microsoft Defender ATP uses automated research. The goal is to significantly reduce the volume of alerts that need to be individually investigated.
The automated investigation uses various algorithms and processes used by analysts (e.g. Playbooks) to investigate alerts and take immediate corrective action to correct violations. This significantly reduces alert volume, allowing security operations experts to focus on more complex threats and other high-value initiatives.
The list of automated scans shows all automatically initiated scans and other details such as status, detection source, and date the scan was initiated. The details are described in the document Overview of Automated investigations.
Microsoft Cloud App Security
Let's briefly come to the term 'Microsoft Cloud App Security', which is described in the document Microsoft Defender Advanced Threat Protection integration with Microsoft Cloud App Security. Microsoft Cloud App Security integrates natively with Microsoft Defender Advanced Threat Protection (ATP).
Once a risky user has been identified, all computers that the user has accessed can be scanned to identify potential risks. Once a risky machine has been identified, all users who have used that machine can be scanned to identify potential risks. So the Microsoft Cloud App Security is a powerful tool for evaluating the logs of endpoints that are forwarded to Cloud App Security.
Similar articles:
Windows Defender ATP EDR for Windows 7/8.1 available
Windows Defender ATP is now Microsoft Defender ATP