 [German]A vulnerability (CVE-2023-5129) exists in the Libwebp WebP library with the maximum possible CVSS index of 10. A heap buffer overflow allows attackers to execute malicious code. Originally, the vulnerability was assigned to the Chrome browser. However, because it affects the Libwebp library, a number of software packages that use this library are affected. Updates have already been released for Chrome and Firefox.
[German]A vulnerability (CVE-2023-5129) exists in the Libwebp WebP library with the maximum possible CVSS index of 10. A heap buffer overflow allows attackers to execute malicious code. Originally, the vulnerability was assigned to the Chrome browser. However, because it affects the Libwebp library, a number of software packages that use this library are affected. Updates have already been released for Chrome and Firefox.
WebP is a modern image format for excellent lossless and lossy compression of images on the web. WebP allows webmasters and web developers to create smaller, richer images that make the web faster. There is a WebP library Libwebp for encoding and decoding images in WebP format.
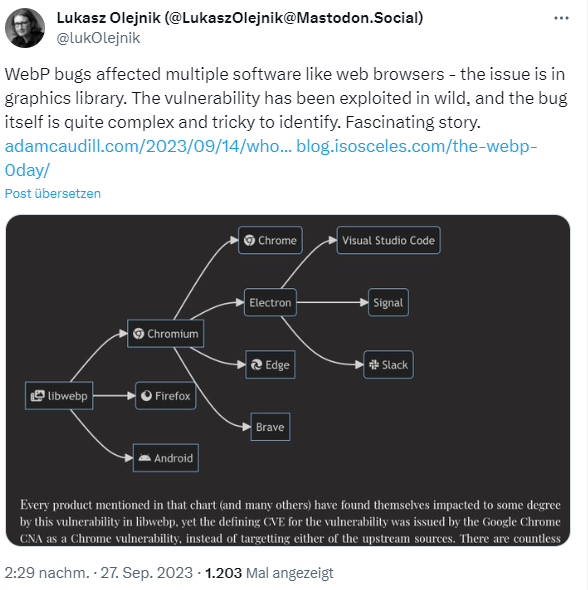
In above tweet Lukasz Olejnik points out that WebP libraries are used in many software products (Chromium, Firefox, Android, Electron framework etc.). Adam Caudill pointed out this issue in his blog post. The vulnerability CVE-2023-4863 has been published for Google Chrome. It is a "heap buffer overflow in WebP in Google Chrome prior to build 116.0.5845.187 that allows a remote attacker to gain out-of-bounds memory access via a crafted HTML page."
However, the same CVE is cited by a number of other vendors because their software is affected. The background: The problem, as outlined above, lies in the libwebp library used by Chromium and a number of other projects. The library is managed by the WebM project, a joint project between Google and a number of other companies.
Firefox, for example, also uses libwebp and is affected by this vulnerability. StackDiary had listed more of these packages in this post in mid-September 2023. 1Password for Mac, Affinity (design software), Gimp, Inkscape, LibreOffice, Telegram, etc. are also among them. According to Google, the vulnerability is actively exploited in WebP (where CVE-2023-4863 is listed).
On The Hacker News there is this article, that points out that the vulnerability in WebP has reached the maximum severity level in the CVSS index. And there reports that attacks are taking place. Users can only check whether the library is used in the programs they use and whether security updates are available.



