[German]Citrix has issued a warning about several security vulnerabilities classified as critical in its Citrix Gateway and Citrix Netscaler ADC. CERT Bund has also published a corresponding advisory. Citrix has released firmware updates to address these vulnerabilities.
[German]Citrix has issued a warning about several security vulnerabilities classified as critical in its Citrix Gateway and Citrix Netscaler ADC. CERT Bund has also published a corresponding advisory. Citrix has released firmware updates to address these vulnerabilities.
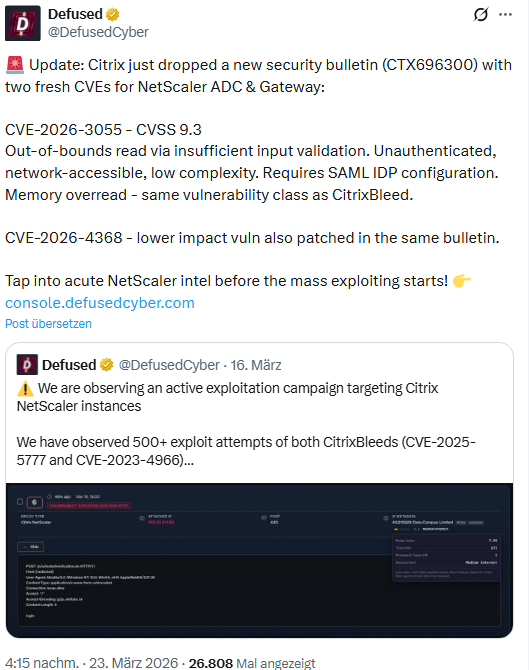
I came across this issue in the following tweet and in addition, a German blog reader pointed out the vulnerabilities (thanks you for that).
These are the two vulnerabilities CVE-2026-3055 and CVE-2026-4368, which affect Citrix NetScaler ADC—an integrated solution for accelerating, managing, and securing web applications—as well as Citrix Access Gateway, a versatile SSL VPN. Citrix has addressed these vulnerabilities in security advisory CTX696300.
- CVE-2026-3055: CVSS 4.0 9.3; Insufficient input validation leads to a buffer overflow.
- CVE-2026-4368: CVSS 4.0 7.7; EA race condition can lead to a user session mixup.
CVE-2026-3055 was discovered internally by the vendor during routine security reviews. It is currently unclear to me why the BSI has assigned a CVSS Base Score of 10.0 to the CVE-2026-3055 vulnerability (Citrix assigns a CVSS 4.0 score of 9.3).
Affected Products
The following versions of NetScaler ADC and NetScaler Gateway are affected by the CVE-2026-3055 vulnerability:
- NetScaler ADC and NetScaler Gateway 14.1 before 14.1-66.59
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-62.23
- NetScaler ADC FIPS and NDcPP before 13.1-37.262
The NetScaler ADC and NetScaler Gateway 14.1-66.54 are affected by the CVE-2026-4368 vulnerability. These vulnerabilities allow an anonymous or authenticated attacker to remotely disclose information and take over a user session.
Updates are recommended as soon as possible
Additionally, there is this Citrix Community post from Saturday, March 21, 2026, with initial information on the topic. As of last Saturday, no attacks exploiting these vulnerabilities were known.
Customers can determine whether their device is configured as one of these elements by checking their NetScaler configuration for the following strings:
An authentication server (AAA-Vserver):
add authentication vserver .*
A Gateway (VPN vserver, ICA proxy, CVPN, RDP proxy):
add vpn vserver .*
Administrators of the affected versions of NetScaler ADC and NetScaler Gateway should install the updated versions of the products listed below as soon as possible.
- NetScaler ADC and NetScaler Gateway 14.1-66.59 and later versions
- NetScaler ADC and NetScaler Gateway 13.1-62.23 and later versions before 13.1
- NetScaler ADC 13.1-FIPS and 13.1-NDcPP 13.1.37.262 and later versions before 13.1-FIPS and 13.1-NDcPP
Both the community post and the Citrix security advisory contain further information on this topic. In the Citrix community post, the vendor also mentions a known issue: In NetScaler firmware 14.1-66.54, there is also a known issue where the STA server binding fails if the explicit path to "ctxsta.dll" is specified in the STA server configuration. This issue occurs when configuring a virtual server or a global binding via the CLI or the GUI.