[German]Microsoft is working on a sandbox mode for applications in Windows 10 Pro and Enterprise so they can be tested in a secure environment. Here is what Microsoft is planning.
[German]Microsoft is working on a sandbox mode for applications in Windows 10 Pro and Enterprise so they can be tested in a secure environment. Here is what Microsoft is planning.
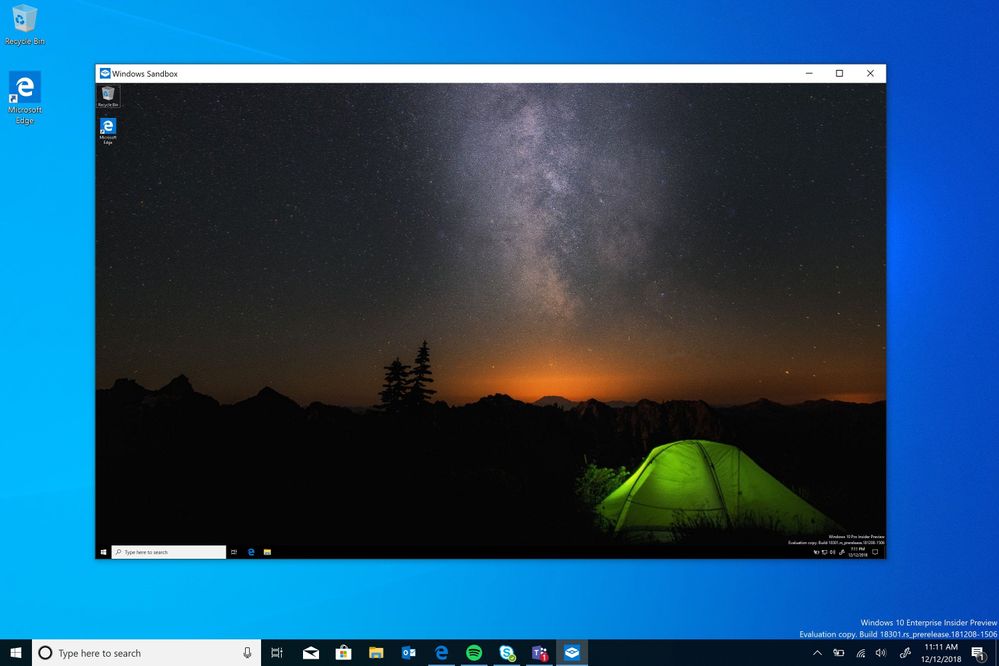
Microsoft just announced the 'Windows Sandbox' in the tech community in the blog post Windows Sandbox as 'a new, lightweight desktop environment designed specifically for secure running applications'.
What is Windows Sandbox?
Probably every Windows user knows this: You have a software that you use for the first time. But one has reservations about executing the downloaded executable file. Cautious users set up a virtual machine to run the software in this environment. Alternatively, some users use solutions like Sandboxie to isolate applications and prevent or roll back changes to the host system.
There have been rumours since the summer that Microsoft is working on a 'security solution' for this purpose. Now the project, which had been started under the name InPrivateDesktop, has been renamed to Windows Sandbox.
Microsoft wrote that they are regularly encounters this situation where untrusted software has to be tested. That's why they've developed Windows Sandbox: an isolated, temporary desktop environment where users can run untrusted software without fear of permanent effects on their PC. Any software installed in Windows Sandbox remains only in the Sandbox and cannot interfere with your host. When you close the Windows Sandbox, all the software with its files and status is permanently deleted.
Windows Sandbox details
Microsoft has announced some details about the Windows Sandbox in its article. Here is an overview.
- The feature is part of Windows 10 Pro and Enterprise, there is no need to download VHDs.
- Each time Windows Sandbox runs, the environment of the software to run is presented as clean as a brand new installation of Windows.
- Nothing remains on the device; everything is discarded after closing the application.
- The sandbox is safe because hardware-based virtualization is used for kernel isolation. This relies on Microsoft's hypervisor to run a separate kernel that isolates Windows Sandbox from the host.
- The whole solution is efficient because the approach uses the integrated kernel scheduler, intelligent memory management, and the virtual GPU.
The requirements to use this feature are quite moderate. The Windows Sandbox thing will be provided in the upcoming Windows 10 version. Here are the details:
- AMD64 architecture (no ARM-CPUs)
- Virtualization features enabled in BIOS
- Minimum 4 GB RAM (8 GB recommended)
- At least 1 GB free hard disk space (SSD recommended)
- At least 2 CPU cores (4 cores with hyperthreading recommended)
A 64-bit CPU and Windows 10 Pro or Enterprise are requirements for Hyper-V. I assume that the CPU must also provide SLAT support. The above requirements should be met by most Windows 10 machines.
How to set up the sandbox
To try it all, install Windows 10 Pro or Enterprise, Build 18305 (not yet released) or later, and enable virtualization. If you are using a physical machine, make sure that the virtualization features are enabled in the BIOS. If you are using a virtual machine, enable nested virtualization with this PowerShell cmdlet:
Set-VMProzessor -VMName <VMName> -ExposeVirtualizationExtensions $true
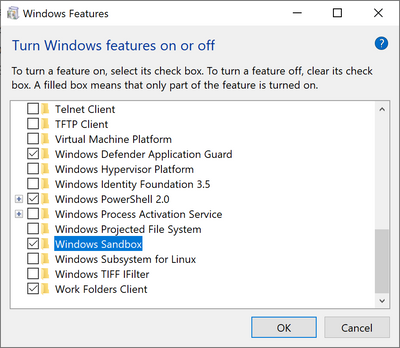
Open Windows-Features, and check Windows Sandbox. Choose OK to install the Windows Sandbox. You may be prompted to restart your computer.
How to run the Windows Sandbox
If the Windows Sandbox has been successfully set up, the feature can be used with the following steps:
- Use the Start menu to find the Windows Sandbox, run it, and allow the user account query.
- Copy an executable file from the host and paste the executable file into the Windows Sandbox window (on the Windows desktop).
- Run the executable file in the Windows Sandbox; if it is an installer, run it and install the application.
- Start the application and use it as usual.
Once you're done experimenting, you can simply close the Windows Sandbox application. All sandbox contents are discarded and permanently deleted. Then make sure that the host does not have any of the changes you made in the Windows Sandbox.
If you are interested in the details and internals, you can find more information in the Techcommunity blog post Windows Sandbox.