![]() [German]A data leak in the photo sharing service of the RICOH/Theta360 resulted, that around 11 million private or public photos and user data could be accessed by anyone.
[German]A data leak in the photo sharing service of the RICOH/Theta360 resulted, that around 11 million private or public photos and user data could be accessed by anyone.
I got informed about that data breach a few hours ago from the research team of the security provider vmpmentor. RICOH is a Japanese company that may be familiar to some readers from RICOH printers.
RICOH Theta360: 360-degree cameras
But RICOH is a diversified electronics company that leads the way in 360-degree cameras. In 2016, the company sold at least 160,000 units. RICOH expects them to maintain their leadership position with a projected sales volume of 250,000 units in 2019.
With such a camera, you can take a 360-degree shot and share it on the Internet. Smartphones with Android or iOS can do the same with the camera apps (I'm already using them). This photos that can be viewed on the Internet, where you can see different views.
Theta360 photo sharing platform
RICOH has also set up the website Theta360.com as a photo sharing platform for its customers. Here is the German edition of this site.

On the page, a camera owner can register to upload the spherical 360-degree photos of the camera and, if necessary, share them publicly or save them privately.
User data publicly accessible
The vpnmentor research teams around the hacktivists Noam Rotem and Ran Locar recently came across a data leak in the photo sharing service of the website Theta360.com. The researchers were able to access data from private and public user accounts. The following data was available::
(Source: vpnmentor)
- The name of the user
- The user name for registering with the platform
- UUID (Universal Unique Identifier) of each posted photo
- caption for each photo
- privacy settings
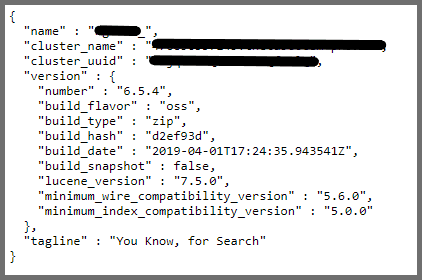
By inserting the UUID of the photos into the Elasticsearch database, the security researchers were able to access all the photos they had uploaded. In some cases, the user names in the database could be easily connected to the user's social media account.
At least 11 million public and private photos are affected by the data leak in the Theta360 photo sharing system, as the security researchers write here. Well, it's not that exciting if a data breach of 'public' photos is discovered. In the Theta360 database, more sensitive data such as location coordinates were also obfuscated. Nevertheless, this is a serious data protection violation that could have far-reaching consequences for victims, if malicious actors had the opportunity to download the database.
But there were also photos in the database that the owners wanted to keep private and had not publicly released for viewing. These photos were also available with further data. And it is certainly not in the sense of a user if private 360-degree photos of his house's interior (see below) are publicly available.
 (Source: vpnmentor)
(Source: vpnmentor)
Many users who privately uploaded photos to the service have not publicly shared personal or private information. For example, some parents choose to keep their children's pictures private because they don't want their children's pictures to be freely available on the Internet. Other parents believe that posting their children's pictures is a violation of privacy.
Cyber criminals also use such data to prepare information for identity theft. But family privacy and identity theft are not the only issues. Among the 11 million contributions on the platform are certainly illegal photos, which must never be published. The publication of illegal photos can have far-reaching consequences for those affected. In some professions, this can cost a user his job, such as a teacher whose nude picture leaked. For others, leaked photos can reveal information about personal matters that are more likely to remain secret.
How the breach was discovered
The vpnmentor hackers discovered the leak in Theta360's database on May 14, 2019 through their web mapping project. Led by Ran and Noam, the research team is searching ports for known IP blocks. Using this information, the activists then find open holes in the company's web systems. They can then search for leaks and other vulnerabilities.
After the leak was discovered, security researchers contacted the database owner to inform them of the vulnerabilities. Theta360.com was notified on May 15, and a response from the vendor came back on May 15. The data base from Theta360.com has been closed for unauthorized access since 16 May 2019.
Now the question remains whether RICOH in Europe is making a notification to the responsible supervisory authorities about the data protection violation in the sense of the DSGVO. And the question arises as to whether German users have been informed. Anyone affected?



