 [German]Check Point security researchers have recently discovered a new variant of mobile malware called Agent Smith that infects Android apps through security vulnerabilities. Currently, about 25 million devices have been infected in silence.
[German]Check Point security researchers have recently discovered a new variant of mobile malware called Agent Smith that infects Android apps through security vulnerabilities. Currently, about 25 million devices have been infected in silence.
As described from CheckPoint, the malware called Agent Smith uses vulnerabilities in Android to infect Android apps on Android 7 and later devices and inject malicious functionality. Currently, Agent Smith is being used to display advertisements about infected apps to gain financial benefits. However, the malware could easily be misused for much more harmful purposes such as banking Trojans or monitoring.
The attack method
"Agent Smith" mainly used three phases in his attack. In the first phase, the attacker tricks users into downloading a dropper application from an app store such as 9Apps. These droppers are usually disguised as free games, utility applications or adult entertainment applications, but contain an encrypted malicious payload. The dropper application then checks to see if popular applications such as WhatsApp, MXplayer, ShareIt, and others from the attacker's default list are installed on the device. If one of the applications is found, Agent Smith attacks these applications at a later time.
In a second phase, after the Dropper has gained a foothold on the victim's device, it automatically decrypts the malicious payload, which is an APK file (Android installation file). The Dropper then abuses several known system vulnerabilities to install the malware without any user interaction.
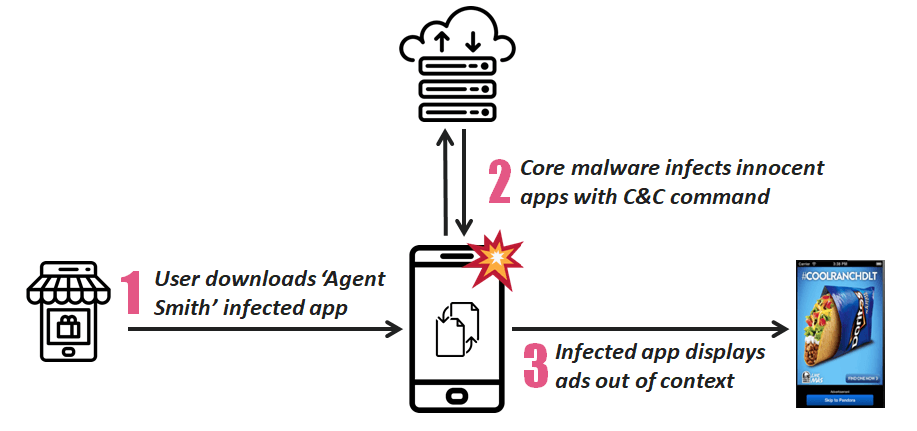
Diagram: "Agent Smith"'s Attack Flow, Source: Check Point
In the third phase, the malware attacks any installed application from a target list present on the device. The core component of the malware extracts the APK file of a particular harmless application, patches it with additional malicious modules, and finally abuses another set of system vulnerabilities to replace the original app in the background with the now malware-contaminated version.
Distribution via App Store
"Agent Smith" was originally downloaded from the popular third-party app Store 9Apps. This store is mainly intended for Indian (Hindi), Arabic, Russian and Indonesian speaking users. Therefore, it is not surprising that the malware reached such a high infection rate in these countries.
Check Point researchers estimate that around 25 million devices are infected. So far, the main victims are located in India, but other Asian countries such as Pakistan and Bangladesh are also affected, as are a significant number of devices in the UK, Australia and the US. (via, via)



