![]() [German]In this blog post, I will quickly summarize important security information that has come to my attention in the last few hours. There are so many topics that the blog would burst with individual contributions. Are violent things like missing security features in certain Microsoft Office 365 variants about RCE vulnerabilities that endanger power plants, etc. are once again all there.
[German]In this blog post, I will quickly summarize important security information that has come to my attention in the last few hours. There are so many topics that the blog would burst with individual contributions. Are violent things like missing security features in certain Microsoft Office 365 variants about RCE vulnerabilities that endanger power plants, etc. are once again all there.
Microsoft Office 365 fails in protection against Emotet
The ransomware Trojan Emotet is often initially spread via spam mail attachments. Administrators should actually secure their Microsoft Office 365 environments against Emotet attacks. The business versions of Office 365 lack an important protective function that can prevent Emotet infections, among other things. This is documented by Microsoft, but largely unknown.
Background: Admins can use group policies to block some things like macro execution in Office. But: When you switch to Office 365, most versions of Office 365 ignore the defaults from Group Policy (without reporting this). German magazine heise has documented it in this article.
RCE bug threaten power plants
Critical remote code vulnerabilities (RCE) in Siemens SPPA-T3000 control system threaten global power plants. A chain of 17 bugs could be exploited to stop power generation and cause malfunctions in power plants..
Critical Remote Code-Execution Bugs Threaten Global Power Plants Seventeen bugs could be exploited to stop electrical generation and cause malfunctions at power plants. https://t.co/HZ7ekdz4pN#News
— Mark Cutting (@phenomlab) February 25, 2020
Phenomlab.com has taken it up in the tweet above and documented it here. The product concerned is the SPPA-T3000, a distributed process control system from Siemens that is used to control and monitor power generation in large power plants in the USA, Germany, Russia and other countries. Siemens provides this security advisory.
Samsung privacy incident on website
These days, Samsung smartphone users received (accidentally) a strange push notification if they were logged on to "Find my Mobile". Some media has reported that last week.
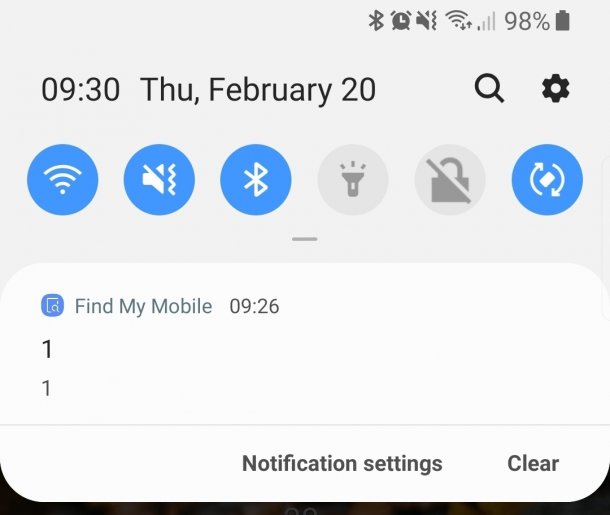
However, it appears that Samsung has had a privacy incident on its website. According to The Register, Samsung has admitted that a "small number" of users were actually able to read other people's personal details after last week's inexplicable Find my Mobile alert.
"A technical error resulted in a small number of users being able to access the details of another user. As soon as we became of aware of the incident, we removed the ability to log in to the store on our website until the issue was fixed."
LTE vulnerability enables identity theft
Security researchers have discovered a vulnerability in the LTE protocol. It allowed them to take over the identity of a smartphone user and, for example, to take out subscriptions at the user's expense. Quote from the security researchers' press release.
An attacker could use the booked services, for example, stream series, but the owner of the victim's mobile phone would have to pay for them," explains Prof. Dr. Thorsten Holz from the Horst Görtz Institute for IT Security, who discovered the security gap together with David Rupprecht, Dr. Katharina Kohls and Prof. Dr. Christina Pöpper. The Bochum team will present the results at the Network Distributed System Security Symposium, NDSS for short, in San Diego, USA, on 25 February 2020.
Details of the attacks are also available on the website www.imp4gt-attacks.net. However, the effort required for the IMP4GT attack (IMPersonation Attacks in 4G NeTworks) is considerable.
Privacy incident at Washington School of Medicine
There seems to have been a privacy incident at the Washington School of Medicine. Now there's a class action suit against those responsible, according to this tweet.
UW Medicine Facing Breach Lawsuit https://t.co/nc267yWfUD
— Infosecurity Mag (@InfosecurityMag) February 24, 2020
Unprotected AWS S3 cloud storage leaks data
Unprotected data storage in Amazon's AWS S3 cloud is probably the source of constant data breaches. Now, more than 30,000 records of inmates in several U.S. states have been leaked via an unsecured and unencrypted AWS S3 Bucket.
An unsecured and unencrypted #AWS S3 #cloud storage bucket unintentionally leaked more than 30,000 records of inmates in several U.S. states. Report: https://t.co/LRpw9UkDpJ
— Trend Micro (@TrendMicro) February 24, 2020
Trendmicro has disclosed the relevant details in the above tweet and linked the article.
KidsGuard app leaked information from Smartphones
The KidsGuard app promises access "to all information" on a target device. This includes access to the user's location in real time, text messages (SMS), browser history, as well as photos, videos and activities of the app and recordings of phone calls.
We just received an email from ClevGuard asking us to delete the two articles we published this week about the KidsGuard stalkerware, which has been used to spy on thousands of victims.
We declined.
Anyway, here's the story they don't want you to read. https://t.co/sSaaRgdm9A
— Zack Whittaker (@zackwhittaker) February 24, 2020
EU Commission and Signal-Messenger
The EU Commission has recommended its staff to use the signal messenger for security reasons. Politico reports this in this article and The Verge has taken it up below.
Signal becomes European Commission's messaging app of choice in security clampdown https://t.co/cw3TozO8rj pic.twitter.com/uMImNHdKFg
— The Verge (@verge) February 24, 2020
Linux: Critical RCE Bug in OpenBSD SMTP Server
Security researchers have discovered a new critical vulnerability in the OpenSMTPD email server (that exists since 2015). An attacker could exploit it remotely to run shell commands as root on the underlying operating system.
Qualys discloses new OpenSMTPD bug (CVE-2020-8794) exploit included: https://t.co/O3Sk8NN6Dy
The previous one was they disclosed in January was exploited in the wild https://t.co/y53tH1kmklhttps://t.co/NN2wsHJZQYhttps://t.co/kV3sn36kfZ
— Catalin Cimpanu (@campuscodi) February 25, 2020
Qualsys has outlined the vulnerability within this plain text article. Bleeping Computer has also an article with details:
New Critical RCE Bug in OpenBSD SMTP Server Threatens Linux Distros – by @Ionut_Ilascuhttps://t.co/rzfy1WElPU
— BleepingComputer (@BleepinComputer) February 25, 2020
OpenSMTPD is present on many Unix-based systems, including FreeBSD, NetBSD, macOS, Linux (Alpine, Arch, Debian, Fedora, CentOS).
Details about Exchange Exploit CVE-2020-0688
The Zero Day Initiative has outlined details how to exploit the recently patched Microsoft Exchange vulnerability CVE-2020-0688.
Want to know how to exploit the recently patched #Microsoft #Exchange CVE-2020-0688? @hexkitchen provides the details on how to take advantage of the fixed cryptographic keys used during installation. https://t.co/N7fds4do5s
— Zero Day Initiative (@thezdi) February 25, 2020



