![]() [German]Security researchers have discovered a huge data leak at the Brazilian company Antheus Tecnologia, which develops and sells biometric solutions in Brazil and abroad. Over 80 million records were accessible, including e-mails from company employees, telephone numbers, 76,000 unique fingerprints and more.
[German]Security researchers have discovered a huge data leak at the Brazilian company Antheus Tecnologia, which develops and sells biometric solutions in Brazil and abroad. Over 80 million records were accessible, including e-mails from company employees, telephone numbers, 76,000 unique fingerprints and more.
The information that security researchers have discovered a data leak at a Brazilian company came to me this week from SafetyDetectives.
Who is Antheus Tecnologia?
Antheus Tecnologia was founded in April 1996 and develops and distributes automated fingerprint identification systems (AFIS), automated fingerprints and other systems such as iris recognition devices.
(Source: SafetyDetectives, Click to zoom)
Antheus Tecnologia states that it is the first Brazilian company certified by the US Federal Bureau of Investigation (FBI) to develop biometric solutions for customers at home and abroad.
16 GByte data leak in identity server
While searching the Internet on one of the company's Elasticsearch servers, the SafetyDetectives team came across about 16 gigabytes of data that was accessible via the Internet. Among the files were highly sensitive personal identification information and biometric details.
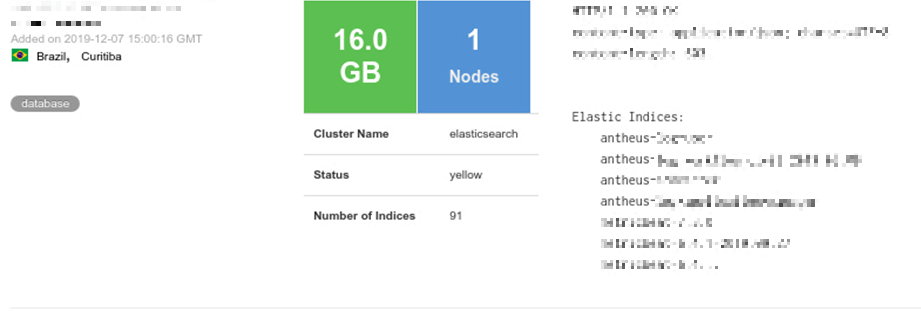
(Source: SafetyDetectives, Click to zoom)
The Antheus server examined by the security team is an identity server. It provides users with access to the system or the ability to register as a new user. The server also stored fingerprint information with at least two "indexes" (out of a total of 91), according to the security researchers. The security team discovered a total of almost 2.3 million data points and estimates that 76,000 unique fingerprints are stored in the database.
What data is affected by the data leak?
The Antheus server stored server and API access logs, but also contained fingerprint data consisting of Ridge Bifurcation and Ridge Ending features – essential components for fingerprint identification and verification.
The team found over 81.5 million records in the unsecured database. Among them were emails from company employees as well as telephone numbers and the 76,000 fingerprints mentioned above.
In addition to the fingerprint information, there were also cases where biometric data, such as facial recognition data, was accessible and retrievable from the database.
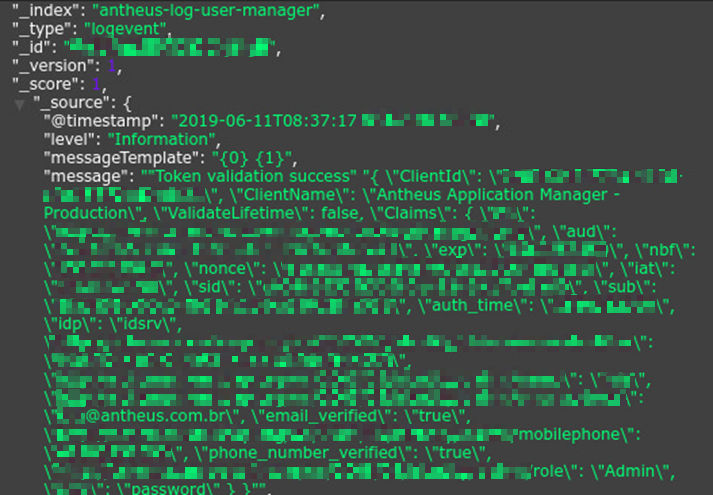
(Source: SafetyDetectives)
In addition to the user data, login information of administrators as well as several e-mail addresses and telephone numbers of company employees were found. That something like this is stored unsecured on a single server is extremely unusual and quite negligent.
Unusual practice and further details
In their article, the security researchers disclose further details. The Antheus Identity Server allows users not only to log in. New users could also register. The practice of allowing access to server data in this way is rather unusual.
The security team has found two indexes in the database that may refer to two different companies that use the Antheus server to store personal information including fingerprint data. They also found data logs related to fingerprint scans. These can be reconstructed from the index numbers stored on the Antheus server.
The security researchers suggest that it might be possible to recreate (or reverse engineer) a biometric image map for a particular fingerprint from the data chains found on the server.
Another vulnerability found
Parallel to the data leakage of the database with the biometric data, the company Antheus Tecnologia had another weakness in its system. This was noticed by the security researchers during their investigation. The company provides services for a national civil identification system in Brazil. This is used to issue driving licences, although the access portal used to create new users is not secure due to a lack of password protection.
Once again, this is 'a full programme' of security breaches – and this at a company that is active in the field of biometric credentials. Details can be found in this blog post.