[English]Security researchers warn that attackers are exploiting the Citrix ShareFile RCE vulnerability CVE-2023-24489 in the wild right now. Citrix ShareFile is a widely used cloud-based file sharing application that is affected by critical remote code execution (RCE) CVE-2023-24489 (CVSS score 9.1). If anyone is using Citrix ShareFile, the vulnerability should be closed urgently.
[English]Security researchers warn that attackers are exploiting the Citrix ShareFile RCE vulnerability CVE-2023-24489 in the wild right now. Citrix ShareFile is a widely used cloud-based file sharing application that is affected by critical remote code execution (RCE) CVE-2023-24489 (CVSS score 9.1). If anyone is using Citrix ShareFile, the vulnerability should be closed urgently.
Citrix ShareFile is a cloud-based solution for sharing files. In early July 2023, vulnerability CVE-2023-24489 was discovered in the customer-managed ShareFile storage zone controller. The vulnerability allows a successful attacker to remotely compromise the ShareFile storage zone controller without authentication. Citrix previously issued security advisory CTX559517 ShareFile StorageZones Controller Security Update for CVE-2023-24489 for this issue in June 2023. This vulnerability affects all managed ShareFile Storage Zones Controllers prior to version 5.11.24. An update is available from the vendor to close the vulnerability.
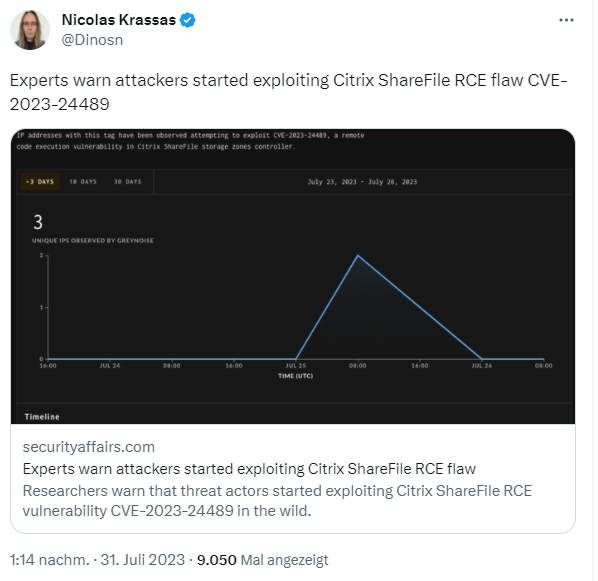
Security Affairs now reports in this article that experts warn that this vulnerability is being attacked in the wild. Security researchers at Greynoise are now warning of the first attempts to exploit this vulnerability in Citrix ShareFile since late July 2023. Greynoise states:
Attackers can exploit this vulnerability by exploiting flaws in the handling of cryptographic operations in ShareFile. The application uses AES encryption with CBC mode and PKCS7 padding, but does not correctly validate the decrypted data. This bug allows attackers to generate valid padding and execute their attack, leading to unauthenticated upload of arbitrary files and remote code execution.
At the time of publishing this post, GreyNoise has observed IPs attempting to exploit this vulnerability. Two of them have never seen GreyNoise prior to this activity.
So anyone using Citrix's solution should urgently review their security around this vulnerability – after all, the MOVEit case where shared file spaces were exploited by the Clop ransomware to rip off data was only a few days ago and is still making waves.