[German]Microsoft mistakenly released the so-called "staging tool" that is used internally to unlock features in Windows 11. The tool was of course immediately withdrawn, but the leak was noticed and a copy of the staging tool is now circulating. Now Microsoft is trying to block the use of the tool. Below, for interested readers, is a brief overview of what's going on.
[German]Microsoft mistakenly released the so-called "staging tool" that is used internally to unlock features in Windows 11. The tool was of course immediately withdrawn, but the leak was noticed and a copy of the staging tool is now circulating. Now Microsoft is trying to block the use of the tool. Below, for interested readers, is a brief overview of what's going on.
What's the staging tool?
Microsoft has designed Windows 11 in such a way that secret features are already integrated into this operating system, but they will only be released to users over time. This way, developers can prepare these features, ship them with Windows updates and unlock them for Windows 11 users via an update at some time.
Microsoft is using an internal tool, the mentioned (secret) staging tool, to enable even such hidden features (e.g. in the context of A/B tests). This allows a developer to selectively enable or disable individual hidden features.
Windows 11 users who want to try something similar can refer to the so-called ViVeTool to unlock hidden features. This tool is developed by "TheBookisClosed" (Albacore), Rafael Rivera and Gustave Monce and is made available on this GitHub page for those interested. Since the developers have to painstakingly figure out all the hidden features including the unlock code, the ViveTool always lags a bit behind.
Staging tool leaked by mistake
I had already noticed it yesterday on the web that Microsoft leaked the staging tool by mistake during it's bug bash for Windows 11 insider preview. I postphoned the article, because there have been more important topics to blog about. But German blog reader Bolko left a comment in the discussion area and gave some additional information (thanks for that), so I'll pull that out. He wrote:
Microsoft has accidentally published a previously secret tool, the "Staging Tool".
It was made available to a tester as part of a bug search ("Bug Bash") in the Feedback Hub and is actually only used for internal tests. Shortly after the accidental publication, the "Bug Bash" post was deleted, hiding the link to the staging tool again.
On Twitter, he showed two screenshots of the now-hidden Microsoft page with the tool and the tool's help output in the console.
He then refers to the following tweet from XenoPanther, who posted the following sceenshotsof this tool on Twitter too.
Tweet 1: Some quests include a valid link to a staging tool that appears to be like vivetool
Tweet 2: It linked to a page where you could download the tool but the link is dead
Tweet 3: Sure! I avoided posting a download (for obvious reasons), but I am OK with posting hashes to avoid people getting infected.
SHA1: b1066e5aac4d4e39534d76a5636564f9b3f3c1f6
The tool was of course immediately withdrawn, but copies are now circulating. The colleagues at German site deskmodder.de have taken the trouble to document the parameters for calling the tool in this post. The same can be found on mspoweruser.com. Now the group around Albacore can experiment with that staging tool an add functionality to the ViveTool. Bolko wrote in his comment:
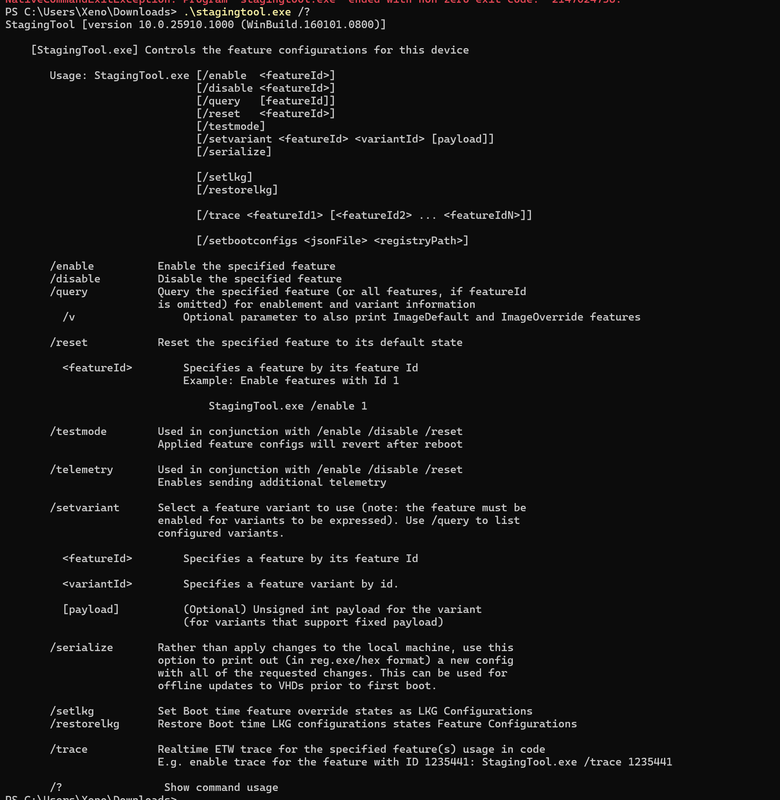
In Windows 10 and 11, a "feature control system" is built in, so that you can enable individual functions or features with the respective "feature ID", which normal users do not get to see or you can also disable previously freely available functions again.
If the ID is known, then with "/enable", "/disable" and "/reset" simply turn on or off the associated feature.
The "Staging Tool" works similar or identical to the two tools "Mach2" and "ViVeTool". One tool lists the feature IDs of the features (Mach2) and the other tool can then turn these features on or off with these IDs (ViveTool).
You probably also need a preview test version (insider channel) of Windows.
github[.]com/riverar/mach2
github[.]com/thebookisclosed/ViVemore informationen on:
winaero[.]com/activate-hidden-features-in-windows-10-insider-builds
winaero[.]com/stagingtool-is-the-official-app-by-microsoft
winfuture[.]de/news,137732.htmlThe feature ID number 44776738 belongs to the AI co-pilot (ChatGPT), you can simply activate this already now in Win11 from build 23493.
Checksum for the "Staging Tool", published by XenoPanther (first hand), so you don't get a fake and don't install malware:
SHA1: b1066e5aac4d4e39534d76a5636564f9b3f3c1f6
twitter[.]com/XenoPanther/status/1687148443381170176The internet of course forgets nothing and so of course there is a mirror of the staging tool posted in the same Twitter thread a bit further down and it currently works with the correct checksum:
local[.]ms/CDN/stagingtool.exeAccording to VirusTotal, the file is clean.
Have fun with it
I'm sure lists of feature IDs will show up soon, and possibly new Windows distributions where you've enabled these hidden features or disabled unwanted features.
I recommend being cautious with the download and use (the danger of catching something "unsightly" is given). Microsoft probably sees this danger similarly and has upgraded Windows Defender accordingly. Bolko wrote about this:
Microsoft has already adjusted Defender.
Today it blocks StagingTool.exe, yesterday it worked like this.
twitter[.]com/WithinRafael/status/1687142813027495936
So it is best to add an exception for the tool in Defender.
Because Microsoft tries to hide the tool, it could be quite useful again.
Mirror 2 for stagingtool.exe with the same clean checksum: ufile[.]io/eh8jcuwp
So it's up to you, to use the inofficial staging tool from Microsoft or the ViVeTool from Albacore mentioned above.