 [German]Singapore-based security vendor Group-IB released a security report that points to specific activity by a group of cybercriminals called W3LL. The cybergang has developed a phishing kit to hijack Microsoft 365 accounts and offers this service to at least 500 other cybergangs through a secret W3LL store. Until now, the provider has been "operating under the radar" of security agencies because customers could only access the offerings by referral. The W3LL phishing tools were used to attack more than 56,000 Microsoft 365 accounts belonging to companies in the U.S., Australia and Europe between October 2022 and July 2023.
[German]Singapore-based security vendor Group-IB released a security report that points to specific activity by a group of cybercriminals called W3LL. The cybergang has developed a phishing kit to hijack Microsoft 365 accounts and offers this service to at least 500 other cybergangs through a secret W3LL store. Until now, the provider has been "operating under the radar" of security agencies because customers could only access the offerings by referral. The W3LL phishing tools were used to attack more than 56,000 Microsoft 365 accounts belonging to companies in the U.S., Australia and Europe between October 2022 and July 2023.
I had seen the post at Bleeping Computer, but was also alerted about the report via a personal message on Facebook (thanks for that). Security vendor Group-IB has compiled its observations in a separate report W3LL done: uncovering hidden phishing ecosystem driving BEC attacks (requires registration), but discloses some details in this post.
The W3LL phishing empire
W3LL is a group of cybercriminals who have specialized in compromising Microsoft 365 accounts via phishing for the past six years. The activity dates back to 2017, but the cybercriminals have managed to sail under the radar until now. Back then, W3LL started with SMTP Sender, a custom tool for mass email spam. Later, W3LL developed and sold a version of the phishing kit targeting Microsoft 365 accounts of enterprises.
Own W3LL Store
Apparently, the cybercriminals succeeded, because they had set up their own, but hidden, underground market called W3LL Store from 2018. In this store, a closed community of at least 500 threat actors could buy a custom phishing kit called W3LL Panel. The phishing kit was designed to surround multifactor authentication (MFA) on Microsoft 365 accounts. The phishing kit also includes 16 other fully customized tools for business email compromise (BEC) attacks as of August 2023.
These tools include SMTP senders (PunnySender and W3LL Sender), a malicious link stager (W3LL Redirect), a vulnerability scanner (OKELO), an automated account discovery tool (CONTOOL), reconnaissance tools and more, the security researchers write. The tools are available on a license basis and cost between $50 and $350 per month.
Over time, the platform has evolved into a full-fledged BEC ecosystem, the security researchers write. Other cybercriminals can book a full range of phishing services there. This ranged from custom phishing tools to additional offerings such as mailing lists and access to compromised servers.
"Customer" support included
W3LL Store provides something like "customer support" via a ticket system and live web chat. Cybercriminals without the necessary knowledge to use the tools can watch video tutorials to "educate" themselves. W3LL Store also has its own referral bonus program (with a 10% commission for referrals) and a reseller program (with a 70/30 split on the profits third-party vendors make selling through W3LL Store).
Referral-only access
Currently, the W3LL Store has more than 500 active users. Anyone who wants to get into the W3LL Store as a new customer must be referred by an existing member. New users have 3 days to make a deposit to their balance, otherwise their account will be deactivated. The developer does not advertise the W3LL store and asks its customers not to spread information about the store and the provider on the Internet.
Successful activities
However, the security researchers from Group-IB probably managed to gain access to the W3LL store, so they were able to have a good look around. Thus, they determined over 3,800 items that were sold via the marketplace between October 2022 and July 2023. Over 12,000 items are currently on sale in the W3LL Store and its turnover for the last 10 months has been estimated at $500,000.
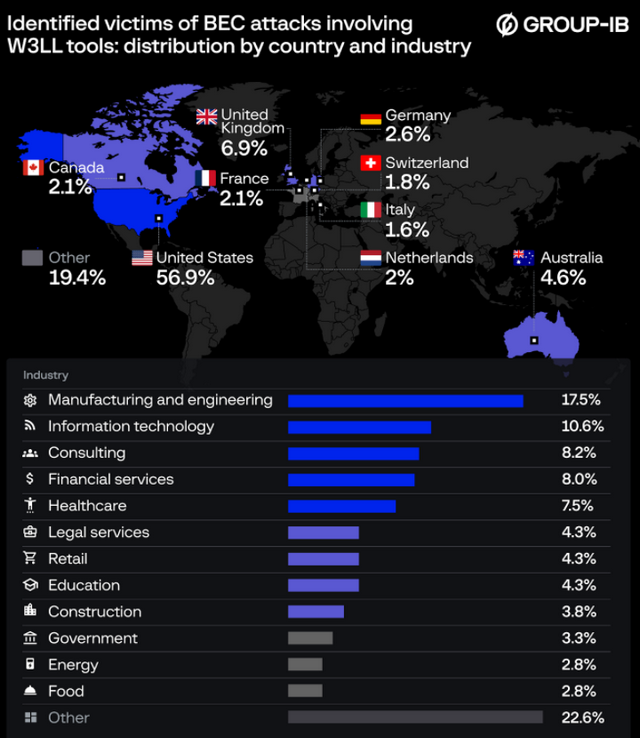
W3LL BEC attacks; source: Group-IB
Group-IB investigators state that W3LL's phishing tools were used to attack over 56,000 Microsoft 365 accounts belonging to companies in the US, Australia and Europe between October 2022 and July 2023. The image above shows the industries and regions attacked. Germany is also among the targeted countries attacked. Group-IB has shared all information gathered about W3LL with the relevant law enforcement agencies.



