[German]Another small addendum from the end of last week. There are several critical vulnerabilities in the Mail Transfer Agent (MTA) and open source mail server. CERT-Bund warns about these vulnerabilities, because attackers could execute arbitrary code via the SMTP service. In the meantime, the developers have provided security updates. Anyone using the Exim MTA as a mail server should urgently patch it immediately.
[German]Another small addendum from the end of last week. There are several critical vulnerabilities in the Mail Transfer Agent (MTA) and open source mail server. CERT-Bund warns about these vulnerabilities, because attackers could execute arbitrary code via the SMTP service. In the meantime, the developers have provided security updates. Anyone using the Exim MTA as a mail server should urgently patch it immediately.
What is Exim?
The acronym Exim stands for EXperimental Internet Mailer, mail transfer agent and mail server. The program was developed in 1995 at the University of Cambridge by Philip Hazel, is free software and evolved from Smail-3. Exim is largely call-compatible with the traditional MTA Sendmail.
The particular strength of Exim lies in a very flexible, yet simple configuration. Thus, Exim can extract data from a variety of data sources/databases and also flexibly process or store them. Furthermore, Exim has built-in regular expressions (PCRE) and a simple but very powerful scripting language. Exim also allows to include a Perl interpreter, whereby own Perl scripts can be used, which then enable e.g. connections to other databases or perform special checks.
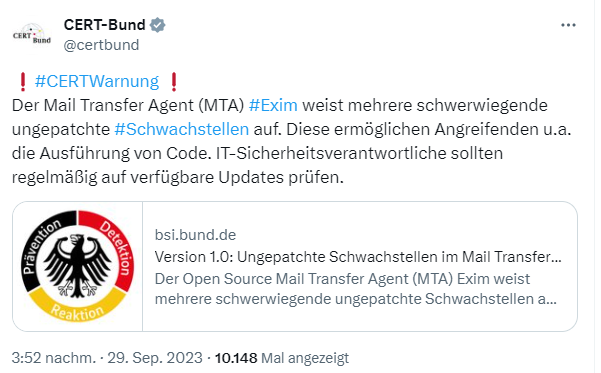
Warning of German CERT Bund
I already came across the warning of the German Federal Office for Information Security (BSI) about (then) unpatched vulnerabilities in Exim at the weekend.
Older versions of the open source Mail Transfer Agent (MTA) Exim have several serious unpatched vulnerabilities. Especially critical is the buffer overflow vulnerability CVE-2023-42115 in the SMTP implementation. This allows a remote, unauthorized, attacker to remotely execute code with privileges of the service account running Exim, if necessary.
According to the Zero Day Initiative (ZDI), the specific flaw exists within the smtp service, which by default listens on TCP port 25. The problem stems from a lack of proper validation of user-supplied data, which can cause a write to extend beyond the end of a buffer. An attacker can exploit this vulnerability to execute code in the context of the service account.
The vulnerability has a CVSS rating of 9.8 ("critical"). Remote code execution could allow attackers to, among other things, leak sensitive data including transport-encrypted emails. All vulnerabilities in Exim were reported to the vendor in June 2022 and published by the Zero Day Initiative on 27.9.2023 after the time window granted for the development of patches had expired.
Patches available
As of September 29, 2023, it was stated that no patches were yet available, even though the flaw was reported a year earlier. At that time of disclosure, it was unknown whether and how Exim version 4.97, which was under development, would close the vulnerabilities (as the BSI warning also states). The only reasonable remediation strategy, according to ZDI, was to restrict interaction with the application.
However, the ZDI announcement is a coordinated release. Exim developers posted the article Exim4 MTA CVEs assigned from ZDI on seclists.org complaining about the communication with ZDI, there were no answers to follow-up questions, making it difficult to identify the bugs. In the meantime, however, most of the vulnerabilities have been fixed:
- CVE-2023-42114 3001 fixed
- CVE-2023-42115 2999 fixed
- CVE-2023-42116 3000 fixed
- CVE-2023-42117
- CVE-2023-42118
- CVE-2023-42119
Regarding the still unfixed vulnerabilities, it is said that they will be patched as soon as the ZDI provides details. This is because, despite the September 2022 announcement, the developers' next contact with the ZDI was in May 2023, following which a bug tracker was created for 3 of the 6 issues. Two of the most serious vulnerabilities (OOB access) have been fixed, and a minor bug (information leak) has also been fixed, the developers say. The fixes are available in a protected repository and can be applied by maintainers of the distribution.
The remaining three issues are disputed or missing information that the developers needed to fix the vulnerability, they write. Seems like a messy story regarding communication. Bleeping Computer has published some more information on the topic.
Conditions for exploitation
In the meantime, Heiko Schlittermann has published some conditions in this document under which the vulnerabilities become relevant.
- 3 of them are related to SPA/NTLM, and EXTERNAL auth. If you do not use
SPA/NTLM, or EXTERNAL authentication, you're not affected.
These issues are fixed. - One issue is related to data received from a proxy-protocol proxy. If
you do not use a proxy in front of Exim, you're not affected. If your
proxy is trustworthy, you're not affected. We're working on a fix. - One is related to libspf2. If you do not use the `spf` lookup type
or the `spf` ACL condition, you are not affected. - The last one is related to DNS lookups. If you use a trustworthy
resolver (which does validation of the data it receives), you're
not affected. We're working on a fix.
The developers are in contact with the main distributions – the fixes should be available there by now.
It will be interesting for "appliances" and software packages where Exim is used. In the Sophos community, there is this forum thread for the XG Firewall. The Sophos UTM and SFOS are both affected by the libspf2 vulnerability (CVE-2023-42118). Customers who use Email Security and have Sender Policy Framework (SPF) enabled are vulnerable to this. As a workaround, it is recommended to disable SPF. Furthermore, they plan to release a SFOS hotfix by October 5, 2023.