 [German]This week, hacks of Santander Bank and the ticket provider Ticketmaster became public. In both hacks, user data was captured on a large scale and is now being sold on underground forums. The story becomes explosive because these hacks are probably made possible by compromised user accounts with the cloud provider Snowflake. The hacker or hackers claim to have obtained the opportunity to attack the two companies via a hacked account of a Snowflake employee. Snowflake denies this and says that weak user passwords of the two victims are the cause of the hack.
[German]This week, hacks of Santander Bank and the ticket provider Ticketmaster became public. In both hacks, user data was captured on a large scale and is now being sold on underground forums. The story becomes explosive because these hacks are probably made possible by compromised user accounts with the cloud provider Snowflake. The hacker or hackers claim to have obtained the opportunity to attack the two companies via a hacked account of a Snowflake employee. Snowflake denies this and says that weak user passwords of the two victims are the cause of the hack.
Hacks at Santander and Ticketmaster
First, a brief review. In my German blog post Cybervorfälle bei Banken: ABN Amro und Santander (Mai 2024), I reported this week that the Spanish bank Santander was the victim of a hack in which millions of pieces of data were exfiltrated from the bank. It involves a database containing 30 million customer records, 64 million account numbers and balances, 28 million credit card numbers, lists of HR employees, and information about customers' citizenship. The data is being offered for sale on a hacker forum for 2,000,000 dollars.
An investigation by the bank revealed that customer data from Santander Chile, Spain and Uruguay was accessed, as well as the data of all current and some former employees. It was mentioned that the hack was possible through unauthorized access to a database hosted by a third-party provider. Santander warned on May 14, 2024 that a database had been compromised. The hackers are offering the 30 million customer records for sale.
Ticketmaster is an American ticket sales and distribution company that operates worldwide. In the German blog post Anbieter Ticketmaster gehackt, mehr als 500 Mio-Nutzerdaten entwendet, I revealed that the provider was allegedly hacked by ShinyHunters. The hackers claim to have stolen 560 million user data, ticket sales, orders, event information and ticket data.
Hacks were made possible via Snowflake
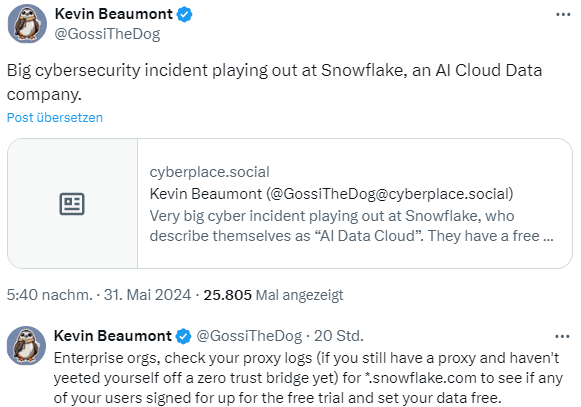
Security researcher Kevin Beaumont takes up the matter in the following tweet and on Mastodon, writing that there has been a "very large cyber incident at Snowflake". Snowflake is a cloud platform (the company calls itself the AI Data Cloud) that is used by 9,437 customers. These include companies such as Adobe, AT&T, Capital One, Doordash, HP, Instacart, JetBlue, Kraft Heinz, Mastercard, Micron, NBC Universal, Nielsen, Novartis, Okta, PepsiCo, Siemens, US Foods, Western Union, Yamaha and many others.
Snowflake offers a free trial version where anyone can register and upload data. And that's probably what the threat actors did. According to Beaumont, the threat actors have been tapping into customer data for about a month using a tool called Rapeflake. He notes that Snowflake had mass data breaches, but no one noticed.
According to Beaumont, it appears that a lot of data was taken "from a number of organizations". He writes on Mastodon that six companies have told him that they are dealing with Snowflake-related incidents in which their data has been copied. Beaumont has now published this article about the case.
Hudson Rock's findings on the hacks
Our colleagues at Bleeping Computer have analyzed the facts in the article Snowflake account hacks linked to Santander, Ticketmaster breaches nd write that the hackers explicitly state that the hacks of Santander and Ticketmaster were made possible via Snowflake accounts. They claim to have hacked into the account of an employee of the cloud storage company Snowflake. The above-mentioned hacks of the cloud instances were then possible. However, Snowflake denies these allegations and states that the recent security breaches were caused by poorly secured customer accounts.
The cybersecurity company Hudson Rock had provided further details in a now-deleted post – so take all details mentioned below with care – on Media is this article about that – and here is another article. By communicating directly with the threat actor behind the massive data breach at cloud storage giant Snowflake, Hudson Rock security researchers have gained unprecedented insight into the devastating impact of Infostealer infections.
The story begins on May 26 in a Telegram conversation with a threat actor who claims to have hacked two large companies, Ticketmaster and Santander Bank. The data of these companies was offered for sale on the Russian-language cybercrime forum exploit[.]in. The database samples provided by the threat actor led Hudson Rock researchers to believe that the data was genuine.
Hudson Rock claims that the attackers also claimed to have used Snowflake to gain access to the data of other well-known companies that use Snowflake's cloud storage services. They include names such as Anheuser-Busch, State Farm, Mitsubishi, Progressive, Neiman Marcus, Allstate and Advance Auto Parts.
To attack, the hackers allegedly bypassed Okta's secure authentication process at lift.snowflake.com by logging into a Snowflake employee's ServiceNow account using stolen credentials. They were then allegedly able to generate session tokens to exfiltrate data from Snowflake customers.
"To put it bluntly, a single access code led to the exfiltration of potentially hundreds of organizations that stored their data with Snowflake, with the threat actor himself stating that 400 organizations were affected," Bleeping Computer quotes Hudson Rock as saying. The threat actor provided Hudson Rock's researchers with a file showing the extent of its access to Snowflake servers. "This file documents over 2,000 customer instances related to Snowflake's European servers," Hudson Rock says.
The threat actor claims that he tried to blackmail Snowflake into buying back the stolen data for $20 million, but the company has not responded to his extortion attempts. Hudson Rock writes that a Snowflake employee was infected by a Lumma-type infostealer in October. The malware stole credentials to the Snowflake infrastructure, as seen in a screenshot shared with Hudson Rock by the threat actor.
Charles Carmakal, CTO of Mandiant Consulting, told BleepingComputer that Mandiant has been supporting Snowflake customers who have been compromised in recent weeks. "Any SaaS solution configured without multi-factor authentication can be massively exploited by threat actors. We recommend that all cloud users implement at least 2-factor authentication and IP-based restrictions," Bleeping Computer quotes Carmakal." Mandiant assumes that threat actors will extend this campaign to other SaaS solutions that contain sensitive corporate data.



