 [German]I'd like to discuss an email I allegedly received from Microsoft regarding an "expiring tenant". Something needs to be ordered because the tenant, which has been inactive for more than 200 days, will otherwise expire. Is it a legitimate mail or phishing, that is the question here? Spoiler: I have failed first to answer the question with 100 % certainty. Then a German blog reader directed me to the right platform – and yes, the phishing mail is a legit Microsoft mail – WTF!
[German]I'd like to discuss an email I allegedly received from Microsoft regarding an "expiring tenant". Something needs to be ordered because the tenant, which has been inactive for more than 200 days, will otherwise expire. Is it a legitimate mail or phishing, that is the question here? Spoiler: I have failed first to answer the question with 100 % certainty. Then a German blog reader directed me to the right platform – and yes, the phishing mail is a legit Microsoft mail – WTF!
Strange mail "from Microsoft"
It was an email that reached me in my free German outlook.com account used for testing and immediately set all the alarm bells ringing. Only a few emails actually arrive on this account – and these usually come from Microsoft (see screenshot below).
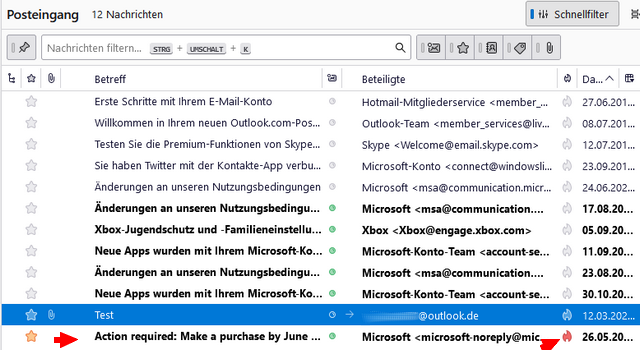
On May 26, 2025, I received an email (bottom entry in the list above), allegedly from Microsoft, with the title "Action required: Make a purchase by June 26, 2025 to continue using your tenant", which I received in a Thunderbird notification. The mail was already classified as SPAM in Thunderbird (see the red arrow in the screenshot above). I had overlooked this at first and quickly wanted to know what was going on, so I looked at the mail.
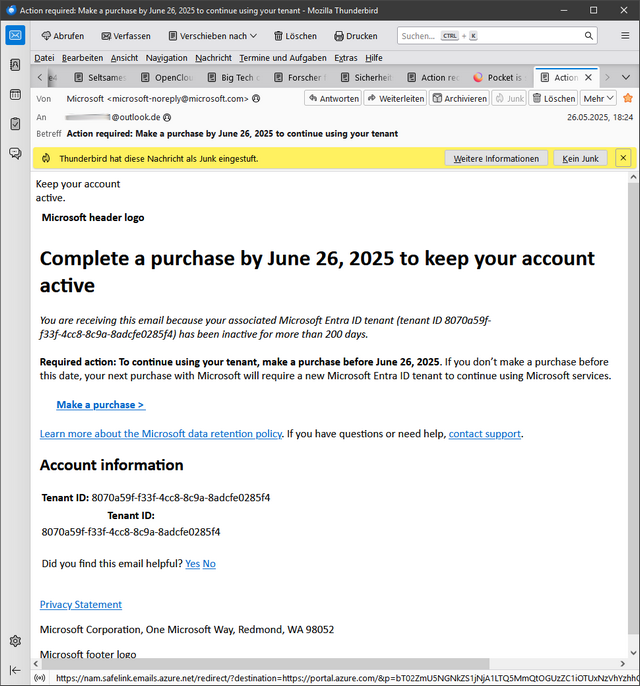
The email informs me that my Microsoft Entra ID tenant with the specified ID will expire because it has been inactive for 200 days. I should make a purchase by June 26, 2025, otherwise a new tenant would have to be purchased. The email also contains links to make such purchases. Here is an excerpt of the relevant information:
Complete a purchase by June 26, 2025 to keep your account active
You are receiving this email because your associated Microsoft Entra ID tenant (tenant ID 8070a59f-f33f-4cc8-8c9a-8adcfe0285f4) has been inactive for more than 200 days.
Required action: To continue using your tenant, make a purchase before June 26, 2025. If you don't make a purchase before this date, your next purchase with Microsoft will require a new Microsoft Entra ID tenant to continue using Microsoft services.
Make a purchase *https://portal.azure.com/
But I don't know, that I use a Microsoft Entra ID tenant and can't do anything with this stuff. On the other hand, Microsoft marketing is in the habit of changing its product names like other people change their underwear. Could it be that some free e-mail account is suddenly sailing as a Microsoft Entra ID tenant? Or was it an Office 365 account that Microsoft unintentionally gave me 10 years ago?
I then realized while writing the German edition of this post: The email was marked as SPAM in Thunderbird (suspicious) – but came through to Microsoft in the outlook.com mailbox – did their SPAM filter possibly goof up, or is the email legitimate? The content of the message didn't look trustworthy to me – why should I buy something if the tenant has been inactive for more than 200 days – a registration should be enough? But it was already midnight when the email arrived, so I saved it and put the analysis on hold. I tried to analyze it while writing this blog post.
What's behind the destination address
In the screenshot above, the Make a purchase target link is displayed in the footer. It is a "safe link" for emails from azure.net, but it has a redirect to a URL of the azure.com portal.
*ttps://nam.safelink.emails.azure.net/redirect/?destination= https%3A%2F%2Fportal.azure.com%2F&p= bT02ZmU5NGNkZS1jNjA1LTQ5MmQtOGUzZC1iOTUxNzVhYzhhOD UmdT1hZW8mbD1idXR0b25fbWFrZV9hX3B1cmNoYXNlX19fXzEw
The redirect is passed a meaningless string (presumably encoded or obfuscated) as a parameter. This is very suspicious and probably the reason for the SPAM flagging by Thunderbird.
According to Microsoft, Safe Links enable the scanning of URLs and the rewriting of incoming email messages during email traffic as well as the checking of URLs and links in email messages, Teams and supported Office 365 apps at the time of clicking. According to this Microsoft support article, the scanning of safe links is in addition to the regular spam and malware protection.
And in this Microsoft document, it says somewhere in the text that if you are not sure about the source of an email, you should check the sender. If an email comes from the Microsoft account team at [any microsoft.com address], you know it's legitimate.
Checking the destination
If you don't look too closely, you could be fooled by the safe link and the URLs. I therefore called up the target URL in the incognito mode of a browser (you shouldn't really do this as an inexperienced user) and was shown the following.
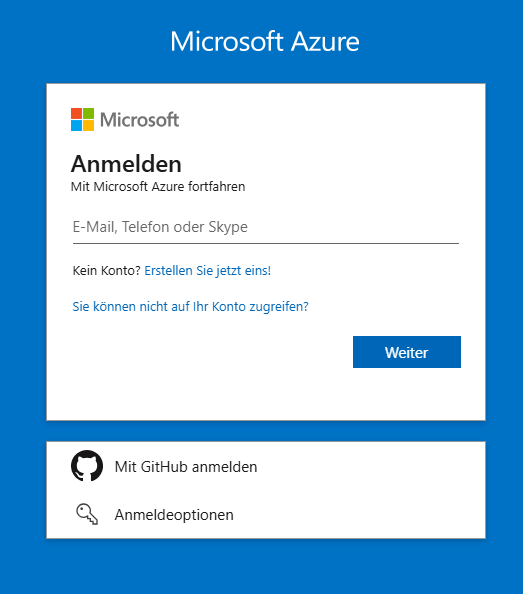
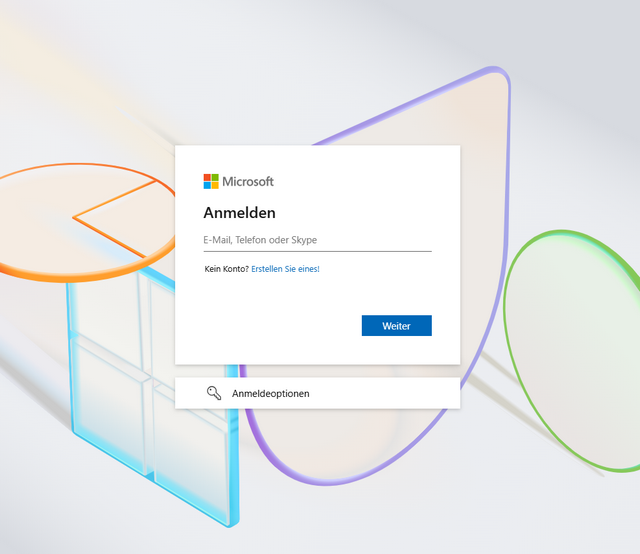
I was redirected to an alleged Azure page to sign in to my Tenant account (see screenshot above). What is immediately disturbing is the blue background – Microsoft has been using a special background for its login pages for several months (see my German blog post Microsoft hat Online-Anmeldung im März 2025 überarbeitet). The login page should now look as shown below.
What does Virustotal say?
As a quick check of such a URL for the target page, I usually ask virustotal.com – there you can copy the URL and get an assessment of x virus scanners. It often works and you get a warning.
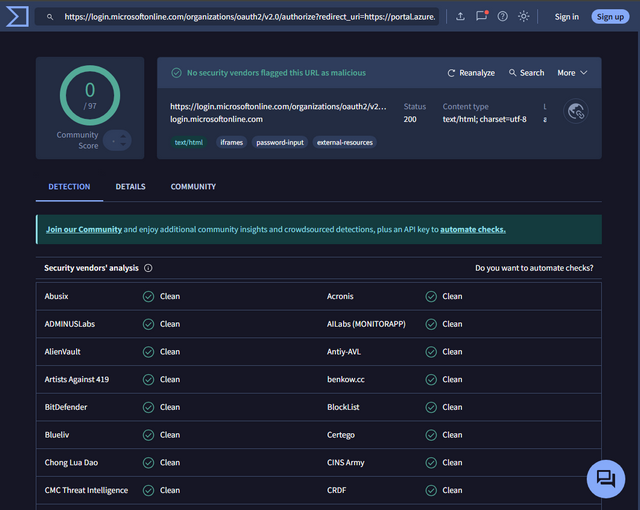
The screenshot above shows that the site is classified as "clean" by 97 virus scanners. So everything is in the green? There is something wrong and I had to assume that virustotal.com was making a mistake.
Check within the developer console
My next attempt was to inspect the login page in the browser's developer console. This request was already acknowledged with a big warning.
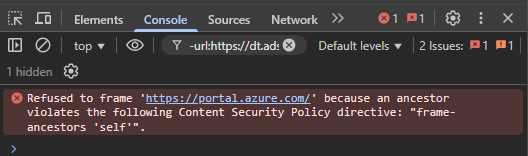
It kind of stinks – the developer console refuses to resolve to the Azure portal.
Is it SPAM?, attempt to analyze
At this point I could have deleted the mail as SPAM. Thunderbird's verdict was clear, but it could still be a false alarm. I therefore wanted to take a closer look at what was going on and prepare the topic in more detail for my blog readers.
What does the header say?
I then inspected the header of the mail in Thunderbird and got the following information.
X-Mozilla-Status: 0001 X-Mozilla-Status2: 00000000 Received: from AS8PR08MB6087.eurprd08.prod.outlook.com (2603:10a6:20b:29c::12) by GVXPR08MB10500.eurprd08.prod.outlook.com with HTTPS; Mon, 26 May 2025 16:24:17 +0000 Received: from DU6P191CA0023.EURP191.PROD.OUTLOOK.COM (2603:10a6:10:540::17) by AS8PR08MB6087.eurprd08.prod.outlook.com (2603:10a6:20b:29c::12) with Microsoft SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id 15.20.8769.24; Mon, 26 May 2025 16:24:16 +0000 Received: from DB1PEPF000509FD.eurprd03.prod.outlook.com (2603:10a6:10:540:cafe::ca) by DU6P191CA0023.outlook.office365.com (2603:10a6:10:540::17) with Microsoft SMTP Server (version=TLS1_3, cipher=TLS_AES_256_GCM_SHA384) id 15.20.8769.25 via Frontend Transport; Mon, 26 May 2025 16:24:16 +0000 Authentication-Results: spf=pass (sender IP is 20.98.194.70) smtp.mailfrom=microsoft.com; dkim=pass (signature was verified) header.d=microsoft.com;dmarc=pass action=none header.from=microsoft.com;compauth=pass reason=100 Received-SPF: Pass (protection.outlook.com: domain of microsoft.com designates 20.98.194.70 as permitted sender) receiver=protection.outlook.com; client-ip=20.98.194.70; helo=mail-nam-cu07-bn.eastus2.cloudapp.azure.com; pr=C Received: from mail-nam-cu07-bn.eastus2.cloudapp.azure.com (20.98.194.70) by DB1PEPF000509FD.mail.protection.outlook.com (10.167.242.39) with Microsoft SMTP Server (version=TLS1_3, cipher=TLS_AES_256_GCM_SHA384) id 15.20.8769.18 via Frontend Transport; Mon, 26 May 2025 16:24:16 +0000 X-IncomingTopHeaderMarker: OriginalChecksum:50D66B43F75B5279726AC9419C9F53151E9D7FF13A469527B23E1F689F621B80;UpperCasedChecksum:47662D1C63A1B049D645E226224F4A4E7A7AEC9E871EE4DD3FAD000A6AFCF88A;SizeAsReceived:831;Count:9 DKIM-Signature: v=1; a=rsa-sha256; d=microsoft.com; s=s1024-meo; c=relaxed/relaxed; i=microsoft-noreply@microsoft.com; t=1748276655; h=from:subject:date:message-id:to:mime-version:content-type; bh=UQhV0VORpQFBtrrT4sem5dhxcqk0olTGAQFIJf8GT6s=; b=tGrkbudiLBVnur49OvxW7Zqc/XBLDDqDMtBGW7Szu0KrTG0dyMX6BLQihIy2A4O9riuT45lNQsO TMPIs27AmAhg6HOpTzD0abf1TjSKhXSj1bv8Y3z8JkjSCaqLVlWgY6280LriDPrdOoFOxXK9n7OTC EYNGOeGBl3nnWE/2+FU= From: Microsoft <microsoft-noreply@microsoft.com> Date: Mon, 26 May 2025 16:24:15 +0000 Subject: Action required: Make a purchase by June 26, 2025 to continue using your tenant Message-Id: <6fe94cde-c605-492d-8e3d-b95175ac8a85@az.eastus2.microsoft.com> Return-Path: azure-noreply@microsoft.com To: *****@outlook.de Content-Type: multipart/alternative; boundary="=-bL7AEVxXhKA6qM/rW3/B9g==" X-IncomingHeaderCount: 9 X-MS-Exchange-Organization-ExpirationStartTime: 26 May 2025 16:24:16.4849 (UTC) X-MS-Exchange-Organization-ExpirationStartTimeReason: OriginalSubmit X-MS-Exchange-Organization-ExpirationInterval: 1:00:00:00.0000000 X-MS-Exchange-Organization-ExpirationIntervalReason: OriginalSubmit X-MS-Exchange-Organization-Network-Message-Id: e5cac02f-5500-49c5-7938-08dd9c71c27f X-EOPAttributedMessage: 0 X-EOPTenantAttributedMessage: 84df9e7f-e9f6-40af-b435-aaaaaaaaaaaa:0 X-MS-Exchange-Organization-MessageDirectionality: Incoming X-MS-PublicTrafficType: Email X-MS-TrafficTypeDiagnostic: DB1PEPF000509FD:EE_|AS8PR08MB6087:EE_|GVXPR08MB10500:EE_ X-MS-Exchange-Organization-AuthSource: DB1PEPF000509FD.eurprd03.prod.outlook.com X-MS-Exchange-Organization-AuthAs: Anonymous X-MS-UserLastLogonTime: 5/26/2025 11:06:05 AM X-MS-Office365-Filtering-Correlation-Id: e5cac02f-5500-49c5-7938-08dd9c71c27f X-MS-Exchange-EOPDirect: true X-Sender-IP: 20.98.194.70 X-SID-PRA: MICROSOFT-NOREPLY@MICROSOFT.COM X-SID-Result: PASS X-MS-Exchange-Organization-SCL: 1 X-Microsoft-Antispam: BCL:2;ARA:1444111002|9400799033|68400799013|22402599018|10300799035|461199028|21080799006|12005499003|1680799057|970799057|5101999024|9000799050|28045499009|1290799030|4302099013|440099028|3412199025|18021999003|33101999003|21101999018|16125499006|17072799003|1360799030|1370799030|1380799030|56899033|1602099012; X-MS-Exchange-CrossTenant-OriginalArrivalTime: 26 May 2025 16:24:16.2083 (UTC) X-MS-Exchange-CrossTenant-Network-Message-Id: e5cac02f-5500-49c5-7938-08dd9c71c27f X-MS-Exchange-CrossTenant-Id: 84df9e7f-e9f6-40af-b435-aaaaaaaaaaaa X-MS-Exchange-CrossTenant-AuthSource: DB1PEPF000509FD.eurprd03.prod.outlook.com X-MS-Exchange-CrossTenant-AuthAs: Anonymous X-MS-Exchange-CrossTenant-FromEntityHeader: Internet X-MS-Exchange-CrossTenant-RMS-PersistedConsumerOrg: 00000000-0000-0000-0000-000000000000 X-MS-Exchange-Transport-CrossTenantHeadersStamped: AS8PR08MB6087 X-MS-Exchange-Transport-EndToEndLatency: 00:00:01.4284569 X-MS-Exchange-Processed-By-BccFoldering: 15.20.8769.014 X-Microsoft-Antispam-Mailbox-Delivery: ucf:0;jmr:0;ex:0;auth:1;dest:I;ENG:(5062000308)(920221119095)(90000117)(920221120095)(90005022)(91005020)(91035115)(9050020)(9100341)(944500132)(4810010)(4910033)(9575002)(10195002)(9320005)(120001); X-Message-Delivery: Vj0xLjE7dXM9MDtsPTA7YT0wO0Q9MTtHRD0xO1NDTD0z X-Microsoft-Antispam-Message-Info: =?utf-8?B?aDc5OVpXM2M0T2syRnZlVkJoZzhqYjV4VmFTK1dqNzB4R0ZHTEc0aVlhUytk?= =?utf-8?B?S1RocS9FQWZ4WGZlRlMwcE4wZEFKS0J5clY3Qm9lbWduclVaOVkwdGQzaTFP?= =?utf-8?B?UE41TytEZW1VSDRzay9DTnl2N2JQNDNFck9tODZnSGxYMWM2NjNjVjFEOXJV?= =?utf-8?B?L0JXWWdwWjd1RmtPdWlYbks2dURKMkNkaWZhTFA1SHFud0p1YlVzY2ZVMDZF?= =?utf-8?B?MTVyQ1ltejZrU1lwejY1SDh3RllPSjliSzBCSWhxQkxKTGVmY2NtaTBTZzFL?= =?utf-8?B?bkxWVFVlUVZQcCt5VnFhRTZkK1h3ZzRsM2tFOUtJUk8wNTFaVWZpYkNYSmQw?= =?utf-8?B?eTJhQXg3WitPZFVoc0lyR240UFp1eU93VVpXS29vUHgyNWEvUkxBUnNPL2M4?= =?utf-8?B?eFFLNURYS0JzMUhGNFlvY3RoZjNhN1R4enRQK05vcHB1dXBjaXJnVzVPNXJN?= =?utf-8?B?Vm5JaGJGMmhmQWJzUWxHZ1BXb1YzK3NIZTNRa3pBQXhaYXllUWpFRGEwWDR0?= =?utf-8?B?TU1UQWVEcUJHZ3M1bkJMODh0cGZVTEtyVTBrY1VrV1N1SEttRzBHNGhXV1Fx?= =?utf-8?B?WHJWZ2tGU2lEMlF6Q3BtbDNEdlovRHhJRVhHZmdaclZmZVBSZVdOdVJpZUZ1?= =?utf-8?B?Qjh4TmR0aVZCUE52dk1UR1dHN3hsQ3l6R2tGaFJ6Q1ZNVWlRZnpvcEc0dnZN?= =?utf-8?B?STZWb20wVU5pUzJCaVFmYithaDNUaysxS3I0R1ZDUi9vYnlBa3ByZGsyRk0r?= =?utf-8?B?a3J1TE9lR2hEc3ZFSVZYZitKNmV3Y3FJSDNvY3Ewc1dSVDcycmZqNUQ1TG1W?= =?utf-8?B?d3VKSGlzaExXa0xjRWl5SUdKYzRSMUtLOHRwSzArclFuMllIdEt0dkZlZUd1?= =?utf-8?B?UElKMkVMRjZpSUxhblBvWWJQcnhyMjF3VUxkMUQ5d3pUNHpWd09jWVYycW00?= =?utf-8?B?elFFR2hJUkUvV3VYTno4UEVoVlpXb25zRWgrZnhzUmJYSi9kb3BvSFFxTjJv?= =?utf-8?B?OWtjYk5JSGh3aFA3Nk5aV0Vva0Q5elptbFZvN2tjVnhYNnNrYmQ0TjRtcGVF?= =?utf-8?B?Y29qSTJrS3FjcXV5WFZqaGIxWk5vQmVXSkRVdnZXUk84Q3YzazhkZlUvL0s2?= =?utf-8?B?ZnVnSHVFMWFMeVIzYlpZTlkyS29HaGJYUEorcHFkZ0wwT3pNcGhocHhsdTBQ?= =?utf-8?B?R2pqZzUzUkFWVlNSemo4cGlGUUc4Zjd4QzFMUFlTUHp6QTNhYVVvb1FuL0Zx?= =?utf-8?B?cXhRNXV6WEdnclVVM2hkVGJuRHBabHhNNGtFdkwvdm5uUTRSU1hMQ2o2S2tZ?= =?utf-8?B?bjFyK0d0U3BZdnBuN1oyYWcrdXIvMFFWOXNKWHFEcnpROENQT3RaZDR1Nncx?= =?utf-8?B?YkRkU05IZVcyME9mZ3l5UmtzU05ERE5BYm5keSthVXUzMlp5bmRlc0Uvd1dP?= =?utf-8?B?ZXN6MkNqTGJZWXVXdGs3WW1zaFpJMmEvR2Rvb3FNbWxnWW9nOWtLNUV5K0NZ?= =?utf-8?B?Q0VwM2toeDhkY1dWU0Exb2wxQkEwVUw1Qy9aK29zSlQyYzBrZktzamlZY3p1?= =?utf-8?B?dlZON1pQSlZkVDZhQW5PN1RhZi9BS2orbDRnUWJoKzMyVG1uT3pzNExscDdR?= =?utf-8?B?N3Y2dDVkNlBzdVVZTkUrdUtjOEtDQVBUUElReFNianRUUVVkRnI4b3MwT0Y4?= =?utf-8?B?LzF1ZFhYNnRpbkt4T3hwWVNEMU5HWitZMm5UMW1QSDdwUlZwTzZ2eDlXR2Fy?= =?utf-8?B?czFrSHpTUEgrTFo5ZW5DQTRkdzJLbTY3ZXFYeEo4K0ZoVGpkRThzbld0R29u?= =?utf-8?B?RmtZVEMrUHp3c203bG9memhsM2N2QkpyelFRUHR6dFprRUQzTEswSDRDSm5k?= =?utf-8?B?UXBGVk8xbTJNa1VucWZTcndKc1ZNRkxIbHdmazVySmwydzU4ODJjcUJrdzVQ?= =?utf-8?B?V2RWOEUvRFpuYldJRE1MSkY2ZlIvcW5ubkRPTkVsU1VRLzhjLzl1bVNIWkhI?= =?utf-8?B?bHRLYTBvV004cmZWNUdRZDlRNVdYVWx4ajBxZnlJODY0aWZ2QmFhcEhVcDZn?= =?utf-8?B?ak8wckVJSUVPaWVuNXRNNCtVbVA0UHJsMFFza0l1NnVqNThPc3dkY1U1MTgv?= =?utf-8?B?R3EzNnhFVGh2d3AzMFFaUmZhM0gvWHFBYW1MYW9rQUNwSEtNMWxyUWtyMEhI?= =?utf-8?B?U1Y4Sk1EWndlWlEvVHpOWmpQN1dkNWlROXJhZjZSVFJGRkVDTm9NUFVQcFdY?= =?utf-8?B?T0l1a3NBRFR3dnJkYUhFRmRIdDM3ZCtES2R2MlZoSndraHZMVXRLU0VONStM?= =?utf-8?B?Y3VsWENPZC82cDdvTFE1ZzBUV0ZUdEZtSytyRFV6T3dVOG0ra1NpQ1BOU0lD?= =?utf-8?B?SEc5cVR6QkVIM21ZUVEzWnNnajBsamNkUG84TG50MzNHRUxwQVFtUDQ2U05v?= =?utf-8?B?dkVRdGc1eFFjYUpWeFhOK0VFeHFQbWlDWmduZ3pjRDFVRnI0ZE4rME1DYWc0?= =?utf-8?B?TlNDZzJBczlMTFp5SDArYUtjakpHOFNrQ2ZJOVZjR1FNZmtyREJnVlRXdHhX?= =?utf-8?B?dTFMR1ZxZDJweEY1MTdzV25kbzRhYk8vWDdnMjc1NW1TSkN2U1dhL3BFeVNO?= =?utf-8?B?ODBqZThiK0RDTVJoVFp5U0hDaVlXMU94RWZhVWY4Nkh6SmF6RE1mSjZxcnBO?= =?utf-8?B?YXo2RjBJemxvN2FBekFjMDdmcm1XeUVQcnM0Nm5PR0h6TGhKNzR5Rm5HOWdo?= =?utf-8?B?ZVJNTmwzUjIwVmRQWWRmUlRqVGFaZENuT2dUTGR5cElvaitKSElUVHlrbGMy?= =?utf-8?B?Z1Q2ZXhUcVlHSjk2aTJYWlhQV29uU2dRZnpuSjVwWUdQM09qcHR0djFrQ1hL?= =?utf-8?B?T293Tzh2em53NjcxZjVCR3ViWDRHMlV1Qk1BQTRKZGE5dWJSY09UM0xKT2Ru?= =?utf-8?B?KytydExEeG11K2RVSXNnSDlCUCtCMlhpRk1TNDJ1ZEpCd3AvM1E9PQ==?= MIME-Version: 1.0
At first glance, everything looks like it was "sent by Microsoft", and the IP address is also assigned to Microsoft in the USA. In other words, the origin is in the Microsoft cosmos. But the sender could have set up a phishing account. The potential phishers have therefore proceeded quite trickily, and an inspection of the header with regard to the question "does the mail come from outside the Microsoft infrastructure" is in vain.
It's probably SPAM – there are more hits
Because of the many inconsistencies I mentioned above, the mail fell into the SPAM category for me. I then did some more searching on the Internet and came across the following reddit.com thread with the same topic.
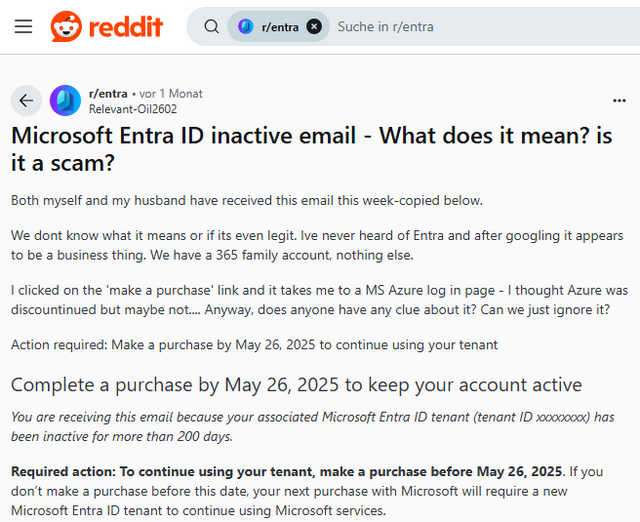
There, the thread starter and other commenters raise similar questions as above. It is a SPAM, scam or phishing attempt, but not badly done. In the thread, users also criticize Microsoft, saying that it is no longer possible to tell whether something like this is SPAM.
Not SPAM? Let me sprinkle a pinch of uncertainty
In the reddit thread above, someone then refers to the Microsoft Q&A post Complete a purchase by January 17, 2025 to keep your account active (titled "AI Skills Fest"), where this is also discussed. Here is the screenshot of the posted question, which is quite similar to my initial email.
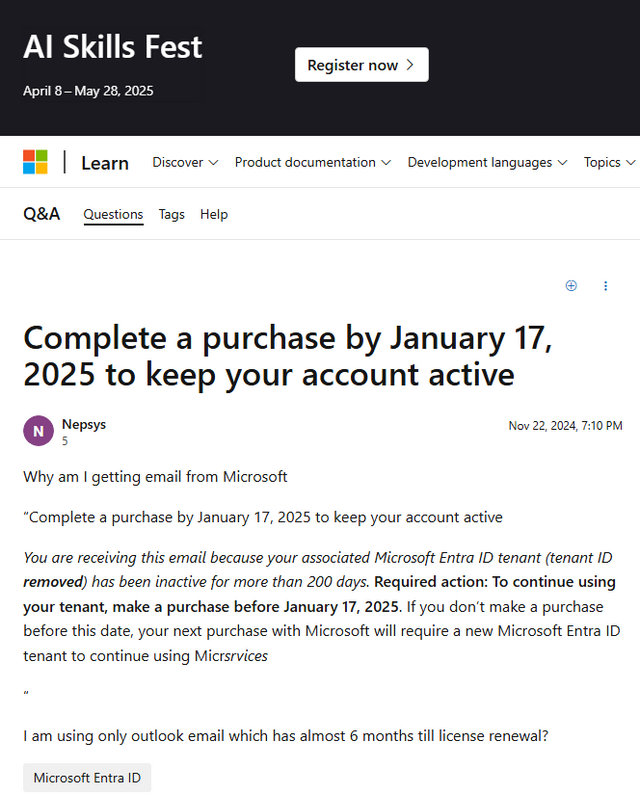
I have extracted the text below – so that it can be found in search engines and linked to the blog post. Mind you, we're talking about an official Microsoft Q&A page here.
Complete a purchase by January 17, 2025 to keep your account active
Nepsys Reputation points Nov 22, 2024, 7:10 PM
Why am I getting email from Microsoft
"Complete a purchase by January 17, 2025 to keep your account active
You are receiving this email because your associated Microsoft Entra ID tenant (tenant ID removed) has been inactive for more than 200 days. Required action: To continue using your tenant, make a purchasebefore January 17, 2025. If you don't make a purchase before this date, your next purchase with Microsoft will require a new Microsoft Entra ID tenant to continue using Micrsrvices"
I am using only outlook email which has almost 6 months till license renewal?
I was quite flattened by the answer – it came twice from a Microsoft moderator and an external moderator:
Hello Nepsys,
Thanks for your question
This indicates that your tenant has been inactive for 200 days.
If you just use outlook, check if you require the Microsoft Entra ID tenant. If it's not essential for your current or future needs, you may choose to let it expire.
If you want to keep the tenant active, consider making a purchase on the account for ur tenant
Follow this link for more information on tenant inaccessibility due to inactivity. https://learn.microsoft.com/en-us/entra/fundamentals/inaccessible-tenant
You can mark it 'Accept Answer' and 'Upvote' if this helped you
Regards,
Abiola
In a nutshell: The Microsoft moderators claim that the e-mail notification on behalf of Microsoft is legitimate and originates from Microsoft. What the fuck! Later I found this Microsoft Answers thread with a similar case – where I posted a link to this blog post.
I took another look at the URL that is resolved by the Safe Mail statement in the URL field of the browser.
https://login.microsoftonline.com/organizations/oauth2/v2.0/authorize? redirect_uri= https%3A%2F%2Fportal.azure.com%2Fsignin%2Findex%2F&response_type= code%20id_token&scope=https%3A%2F%2Fmanagement.core.windows.net%2F%2F user_impersonation%20openid%20email%20profile&state= OpenIdConnect.AuthenticationProperties%3D uxz6z5N_5Ixhg9N6BGUaMC3bGk2UKXtrL00guLosODZORYKXhxSQL3urwjUIOcZ qPYwWPOAJpk6na8kG23KXG0H50ONs2I0dkFR4Dpb3PgHVYLnAgf2a69keIc0QhHB jYznmS8iD0kDD4oudMjSo0810C1CHxHqIAOoS__Iy9eRAncFBFmWYqDooGAq7ajd gV6FXIWzWL9NE0cTBBlVceJFBfQr0YgeqiIKnV2oX3K2RaQQCrT9tvNlyexWpy1 GXTLFLFp_EkwDqHVqy7YJHNLGd_jnXLKBkp6DNkZJpBmfp05j4YDgaqWGUCYfDQ2 E3AFB9O5A0OO_c5bBdE2vjFzyJQl1u2pGvKExReDGdIsYKl9Oa27RDV5sONadoTaK h6CvCnBIs_V3NdADIAAL3JOqkRqfqPVWwraSmamGim02mKosJyJN3XBKFnm7Lm7z_Ca 09oIleggW48zbqwwROR82XQhXe9ZMGxPTM0YCEXAY&response_mode= form_post&nonce=638838932065190836.OWYyMjQzZWEtNGU1Yy00Nzc1LWI3Zm QtYjk2MTQwZmM3YWIzZjk5Yjg2N2QtMTkyZi00OTlkLThjMjUtMWMzMDhlYzJlZTNm& client_id=c44b4083-3bb0-49c1-b47d-974e53cbdf3c&site_id=501430& client-request-id=21b8db4f-7fca-4c1e-97a7-07a85651f29c& x-client-SKU=ID_NET472&x-client-ver=8.3.0.0&sso_reload=true
The domain microsoftonline.com gehört belongs to Microsoft, as do the portal.azure.com and windows.net. What is going on in the parameters is not clear to me ad-hoc (apart from the fact that a form is to be displayed for registration). Who comes up with something like this?
Final thoughts
I have broken down the simple email in the post above, but at this point I am not sure whether it is not something legitimate from Microsoft. Maybe I've missed something and a blog reader can shed some light on it.
But this case leads me to the question: "How broken is the Microsoft eco-system?" when I, as a somewhat advanced recipient of such an email, can no longer recognize whether it might be something legitimate after all. This stuff has become so complex that a normal user has hardly any chance of judging whether an email is SPAM or really comes from the alleged sender.
Addendum: It's from Microsoft – WTF!
After publishing the German edition of this blog post, reader Mom20xx left this comment (thanks) and told me, to check the tenant ID at Tenant ID Lookup. Then "things got really stinky" – here is the result of the test:
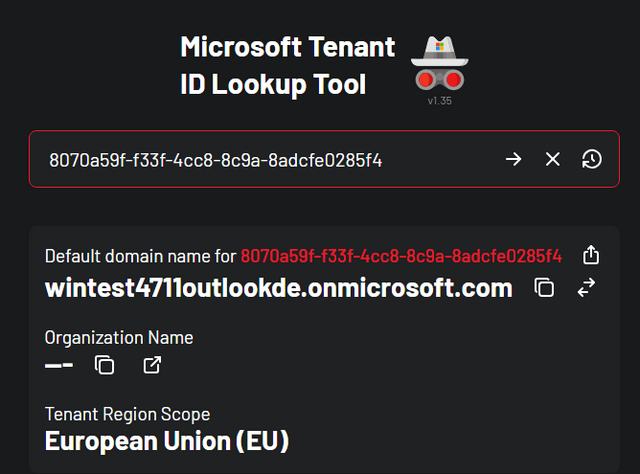
It is my outlook.de test account that is specified. However, this is now somehow assigned to an onmicrosoft.com tenant. So the mail comes from Microsoft and the sender knows the tenant ID. This leads me to the following statements:
- How does Microsoft get to write such a cryptic mail to users with a private outlook.com/.de account?
- How does Microsoft get to ask users to buy something when a free email account is supposedly no longer in use?
- How does Microsoft come to the assumption that the account has been unused for more than 200 days – when this message is displayed in Thunderbird (i.e. has been retrieved from the account)?
- Who at Microsoft is responsible for this implementation? I don't have an Azure account and probably can't sign in. And all these redirect URLs is a case of can't do.
You'd think Microsoft had either been hacked – or that they've totally lost control of their cloud stuff. One reader said it's because of the topic from my German post Microsoft bereinigt Millionen Cloud-Tenants nach Storm-0558-Angrif, which "was hacked" – but then drops "lost control of their cloud stuff or never had". WTF! Or how do you see it?




Hi,
Thanks for your elaborate write up. I received the same email this morning and started a similar investigation and came to the conclusion that I need more time and more advanced tools to continue my investigation. Your write up saves me some of that work. I totally agree with you: "'How broken is the Microsoft eco-system?' when I, as a somewhat advanced recipient of such an email, can no longer recognize whether it might be something legitimate after all."
As a professional Azure cloud engineer, I have created some personal accounts/tenants, so it *could* be a legitimate email. But something doesn't feel right about the email. Using the tenant id lookup tool (thanks for the link – couldn't find it for my initial assessment) gave me the answer I was looking for: in my case it maps to 'Duhmeaufde353.onmicrosoft.com' which means absolutely nothing to me.
So for me it is clear now: it is fake.
Thanks for the write up and the tenant id lookup tool link.
I've come to the conclusion that it's fake. We received the same e-mail at work (a random employee), and the tenant id lookup tool showed some onmicrosoft account with company name + a random number as the owner.
This is a legitimate e-mail from Microsoft.
My best guess is that you might have created a 365 (trial) tenant at some point in the past. Maybe unknowingly whilst testing something.
I think your assumption that this has to do with your free outlook.de account is incorrect.
I've done some research and it appears to be legit.
The IP of the sender's server is correct, the link to the Microsoft site in the content etc. – it all looks fine.
Admittedly, I don't recognise the tenant name ***.onmicrosoft.com – but I think I already know why.
Well (in my opinion) the reason we are all getting it now is the passage of time. Exactly since COVID started – and we all had to provide remote working tools quickly. Many times testing on ad-hoc tenants set up. And this has now come back. IMHO.
Thanks for your feedback. The last sentence doesn't fit for me – I've never tested a tenant from Microsoft during covid – and the tenant ID points to my free outlook.de mail account.
My result matches the company name I invented for my free personal MS Teams account, indeed "during COVID." I don't use it, so this tracks.
I got the same email this morning and came across this email string within 15 minutes of searching.
Thanks for posting this string.
Since I received it on an apple computer, I am able to view the entire header. It states the return path and that the address is not allowed to send mail from Microsoft.
Return-Path:
X-Spf-Check: 45.93.148.2 is not allowed to send mail from microsoft.com
Then it goes through the process of spoofing the address, similar to the sexploitation emails.
I am treating this like the spam it is.
Thanks
I haven't as exhaustively researched this as much as the poster or other commenters, but I just received the same email and I've done some cursory checks and actually logged into my account through the link in the email, and it did take me to my company's old MS account. However, we haven't used any MS cloud services in many years, and our developer account hasn't been active for many years either. So I have a couple theories which I think are quite possible:
1. Microsoft is prepping to purge a LOT of old accounts which haven't logged in for a long time, and THIS is some engineering manager's idea of a message which will make sense to the account holders that they are about to be purged. These could be users of ANY MS product at ANY point in the past (all emails say "more than" 200 days — yeah, probably MUCH more!). With the name changes of MS products, users who haven't use their cloud products in forever don't even know what an 'Entra ID' even is (I didn't and had to look it up, but I'm also not an Azure user). So theory one is that this is a legit message which fails horribly at communicating an impending account purge.
2. (More likely, in my opinion) Microsoft is desperate to scrounge up more cloud/Azure business, so this is a 'marketing' driven email which is intended to get previous account holders to log into their accounts and then maybe buy some new service while they're there — much like businesses send out coupons for a 'free' item or some in-store only promotion to get people in the door in the hopes that a significant percentage will buy something. All of the email recipients I've seen commenting on this appear to be associating the account in the email as one that has long been disused, and my guess is that MS just mass emailed ANYONE who at one time had an account but haven't used it recently and sent this 'scare' email to them all to get them to log in and (hopefully) buy something. [They didn't seem to mind all of the other '200 day' windows expiring without me using their services, so why the sudden concern now??]
Maybe it's actually BOTH! (Kill two birds with one stone.) Either way, it's a crappy and poorly communicated way to accomplish either of the above objectives, but that really wouldn't surprise me coming from Microsoft. So I think it is actually a legit message which is poorly communicating a rather benign and unimportant deadline to a bunch of people who don't really need to take any action. Good riddance. PLEASE purge my non-used account and go away!
It's insane! If your assumption is true, that they are trying to kill old account, why they require an "order"? That's a no go!
Yes, I'm pretty sure, it is legit.
I my case I registered a new Azure account during a training on the subject of Azure about a year ago, using my personal @outlook.de Microsoft account.
Entering the tenant ID from that obscure mail into the lookup tool it resulted in which is the domain of my Azure tenant from that training. As I never used this Azure account again after the training it does make sense. To be completely sure I would have to try to log in to that tenant, but I'm too tired now… ;-)