[German]Two critical vulnerabilities have recently been disclosed in the Ubiquiti UniFi Network Application. Vulnerability CVE-2026-22557 has a CVSS score of 10.0 and can be exploited without authentication to take over an account. CVE-2026-22558 has a CVSS score of 7.7 and allows for privilege escalation.
[German]Two critical vulnerabilities have recently been disclosed in the Ubiquiti UniFi Network Application. Vulnerability CVE-2026-22557 has a CVSS score of 10.0 and can be exploited without authentication to take over an account. CVE-2026-22558 has a CVSS score of 7.7 and allows for privilege escalation.
Ubiquiti manufactures and distributes both wireless and wired data communication products for businesses and households under various brand names. For example, UniFi Access is a door access control solution from Ubiquiti.
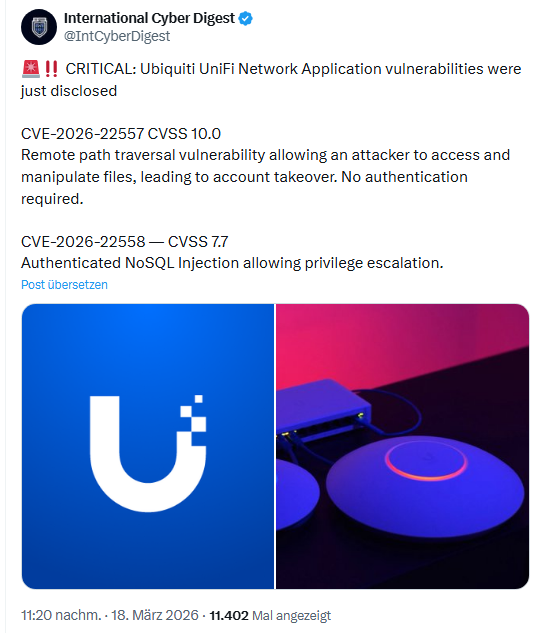
UniFi Vulnerabilities (CVE-2026-22557, CVE-2026-22558)
On March 18, 2026, two vulnerabilities, CVE-2026-22557 and CVE-2026-22558, were discovered in the Ubiquiti UniFi Network Application. I came across this information via the following post on X. Ubiquiti published a security advisory on March 18, 2026.
- CVE-2026-22557: A remote path traversal vulnerability in the UniFi Network Application, rated 10.0 on the CVSS 3.1 scale. This vulnerability allows an attacker to access and manipulate files, which could lead to account takeover. No authentication is required to exploit this vulnerability.
- CVE-2026-22558: EAn authenticated NoSQL injection vulnerability rated with a CVSS 3.1 score of 7.7. The vulnerability allows an authenticated attacker to escalate privileges.
The following UniFi Network Application versions are affected by this vulnerability:
- Official Release: UniFi Network Application (Version 10.1.85 and earlier)
- Release Candidate: UniFi Network Application (Version 10.2.93 and earlier)
- UniFi Express (UX): UniFi Network Application (Version 9.0.114 and earlier)
Ubiquity has released the following versions of the UniFi Network Application to address the vulnerabilities.
- Official Release: Update the UniFi Network Application to version 10.1.89 or later.
- Release Candidate: Update the UniFi Network Application to version 10.2.97 or later.
- UniFi Express (UX): Update UniFi Express firmware starting with version 4.0.13, which updates the UniFi Network Application to version 9.0.118 or higher.
Details and download links can be found in the Ubiquity security advisory.