![]() [German]After the first malware attacks using the BlueKeep vulnerability have been found in the wild (see Windows: first BlueKeep Metasploit in the wild), Microsoft and the Australian government are intensifying their warnings.
[German]After the first malware attacks using the BlueKeep vulnerability have been found in the wild (see Windows: first BlueKeep Metasploit in the wild), Microsoft and the Australian government are intensifying their warnings.
Short review of BlueKeep
The BlueKeep vulnerability in the Windows RDP service threatens unpatched systems from Windows XP to Windows 7 and their server counterparts. I had been warning about the BlueKeep vulnerability for months (see BlueKeep warning: Exploit might come soon?). It seems, however, that the BlueKeep vulnerability is difficult to exploit in practice. This is the only way to explain that this issue has been quite quiet so far, although there is a publicly available metasploit (see Windows: Bluekeep Metasploit released in the wild). But that could change now.
Last week the picture has changed. Security researcher Kevin Beaumont had set up a worldwide network of honeypots for the RDP vulnerability following the discovery of the BlueKeep vulnerability and the availability of the first exploits. On Saturday Beaumont reported that its EternalBlue RDP honeypot suddenly showed BlueScreens.
When security researchers looked at the BlueScreen crash dump, it became clear that someone was trying to exploit the BlueKeep vulnerability. MalwareTech security researchers confirmed that the kernel dump contained traces of a metasploit to exploit the BlueKeep vulnerability (or at least something based on it). It is probably an attempt to install a crypto-miner on Windows machines via the vulnerability. I had collected details in the blog post Windows: first BlueKeep Metasploit in the wild.
Warning from the Australian authorities
An article at Bleeping Computer reveals, that australian Cyber Security Centre (ACSC) of Australian Signals Directorate warns together with partners from the states, companies and individuals from threats by the Ransomware Emotet and from exploiting the BlueKeep vulnerability. Both threats were active in the wild.
The ACSC apparently took up the above-mentioned findings and calls on users to be vigilant. Attackers have begun to exploit the Windows BlueKeep vulnerability to attack unpatched systems and infect them with coin miners.
Regarding the Emotet campaigns, the ACSC writes that these have slowly decreased compared to the end of October last week. However, emotets still pose a significant threat to businesses and the general public. More details can be found at Bleeping Computer.
Microsoft also warns again against BlueKeep
The above-mentioned discovery of malware infecting honeypots with a crypto-miner via the BlueKeep vulnerability is also a wake-up call for Microsoft to finally patch its system.
While we currently see only coin miners being dropped, we agree w/ the research community that CVE-2019-0708 (BlueKeep) exploitation can be big. Locate and patch exposed RDP services now. Read our latest blog w/ assist from @GossiTheDog & @MalwareTechBlog https://t.co/y1NgN5WVu8
— Microsoft Security Intelligence (@MsftSecIntel) November 7, 2019
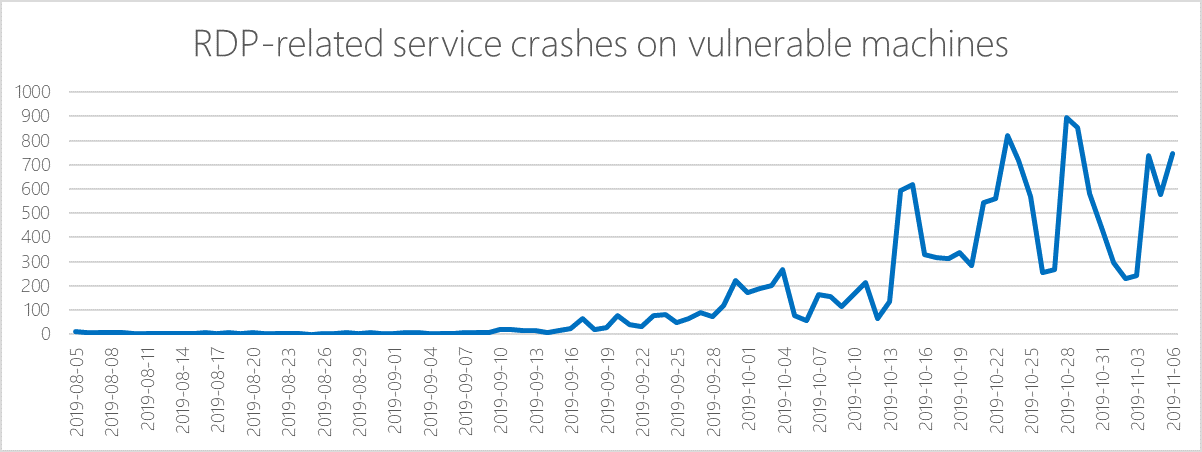
In the tweet above, Microsoft security specialists point to MalwareTech's analysis of the BlueKeep attack and recall that patches are available for the RDP vulnerability. Microsoft has summarized its findings in this blog post (Bleeping Computer picked it up here). The following chart shows the increase in attacks on BlueKeep honeypots.
Figure 1. Increase in RDP-related service crashes when the Metasploit module was released Source: Microsoft
Background: BlueKeep vulnerability
I had reported about the BlueKeep vulnerability CVE-2019-0708 in several blog posts. An explanation of the vulnerabilities can be found in the blog post Security Critical update for Windows XP up to Windows 7 (May 2019).
There is a patch, but it has not been installed on all systems (see Windows: What about the BlueKeep vulnerability in July 2019? ). In my blog post How To: BlueKeep-Check for Windows, I explained how a system can be scanned both locally for installed patches and in a network for vulnerabilities.
Similar articles
A threat actor scans Windows systems for BlueKeep vulnerability
BlueKeep: Windows Remote Desktop Services vulnerability exploits status
Critical update for Windows XP up to Windows 7 (May 2019)
Nearly 1 million Windows machines with BlueKeep vulnerability
BlueKeep vulnerability: Microsoft warns about a wormable malware epedemia
BlueKeep: Patch for pirated copies; SSL tunnel as a risk factor
Windows: Bluekeep Metasploit released in the wild
BlueKeep warning: Exploit might come soon?
How To: BlueKeep-Check for Windows
Windows: first BlueKeep Metasploit in the wild