![]() [German]The data leak (PussyCash) that security researchers have come across is a database of over 875,000 files that reveal very personal information (from ID card scans to addresses and birth certificates, credit cards, etc.) of erotic models active on adult sites. I was just made aware of this case by the security researchers of vpnMentor.
[German]The data leak (PussyCash) that security researchers have come across is a database of over 875,000 files that reveal very personal information (from ID card scans to addresses and birth certificates, credit cards, etc.) of erotic models active on adult sites. I was just made aware of this case by the security researchers of vpnMentor.
PussyCash: 'Cam' affiliate network
PussyCash is a 'cam' affiliate network that offers websites for adult models with adult content through brands like ImLive. PussyCash hosts affiliate programs for several adult websites and pays webmasters for the traffic that is sent to the websites via banners and exit traffic. They boast 66 million registered members in their webcam chat arena ImLive alone.

(Source: vpnMentor)
Other websites include Sexier.com, FetishGalaxy, Supermen.com, Shemale.com, CamsCreative.center, forgetvanilla.com, idesires.com, Phonemates.com, SuperTrip.com and sex.sex.
Partners listed on the PussyCash website include BeNaughty, Xtube and Pornhub. The owner of ImLive and PussyCash is officially listed as I.M.L. SLU, a company registered in Andorra.
The data leak
The vpnMentor cyber security research team, led by Noam Rotem and Ran Locar, has discovered an open Amazon S3 bucket on an Amazon server in Virginia. There 19.95 GB of data related to PussyCash and the underlying network were openly accessible and viewable.
More than 875,000 files were stored on the S3-Bucket. The files contained marketing material, clips and screenshots from video chats, etc. But the more explosive part is the fact that thousands of folders of models using the platform are openly accessible. These folders also contain pictures and scans of their passports, ID cards, social security cards, credit cards and much more. Here is the list of the models' data:
- Full name
- Date and place of birth
- Status of citizenship, nationality
- Passport/ID number
- Passport issuance & expiry dates
- Nationally registered gender
- Identity card photo
- Personal Signature
- Full names of parents
- Fingerprints
There are also country-specific details (e.g. emergency contact information for British citizens). All the cutlery you'd need for identity theft – cyber criminals can use this data to open accounts in the name of the person concerned and much more.
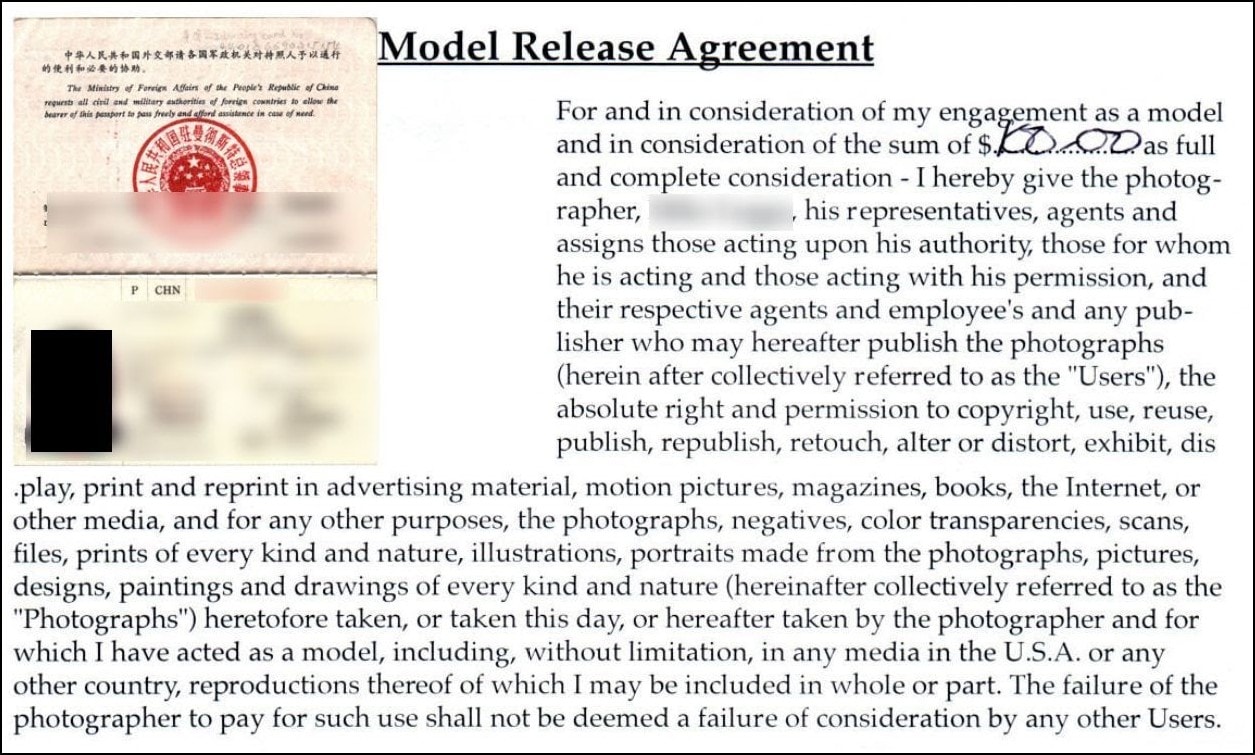
(Modell Agreement, Source: vpnMentor)
The files also included scans and photos of driver's licenses, US military identification cards, credit cards, model contracts, birth certificates, resumes and much more. The following tweet shows a copy of a US driver's license – more scans are available on this vpnMentor page.
Adult performers, heads up!
A data leak exposed personal identifiable information of thousands of cam models. If you had an account with @ImLiveCom or other @PussyCash web properties going back to the last 15 years, your data may have been exposed.https://t.co/ZEYn9WrzLX pic.twitter.com/Sai3pmhxSh
— Chloe Lewis (@newchloe18) January 15, 2020
The models world wide are thus made virtually transparent.
A GDPR case?
It seems that the leak was caused by one of the numerous brands of PussyCash. Since the owner of ImLive and PussyCash is officially registered as a company in Andorra, he might be subject to the GDPR. This makes the story interesting also from this point of view, because there might be a bigger fine. Here still the chronology of the case:
Date discovered: January 3rd, 2020
Date of notification of the company (PussyCash & ImLive): 4 January 2020
Data Amazon notified: January 7, 2020
Date of ImLive's response: 7 January 2020
Date of the action: 9 January 2020
The provider PussyCash (and their data protection officer) has probably not reacted at all to the reports of the security researchers, as they write here. Only ImLive finally replied to one of our e-mails and declared that they would take care of it and forward the information to the technical team of PussyCash. More details can be read in the vpnMentor article.



