![]() [German]The Microsoft 365 security team points out a malware campaign called Adrozek. The malware targets popular browsers such as Google Chrome, Microsoft Edge, Firefox, etc. and tries to manipulate the browser in such a way that advertisements are played during a search. Through this approach, those behind it try to generate revenue. Europe seems to be particularly affected.
[German]The Microsoft 365 security team points out a malware campaign called Adrozek. The malware targets popular browsers such as Google Chrome, Microsoft Edge, Firefox, etc. and tries to manipulate the browser in such a way that advertisements are played during a search. Through this approach, those behind it try to generate revenue. Europe seems to be particularly affected.
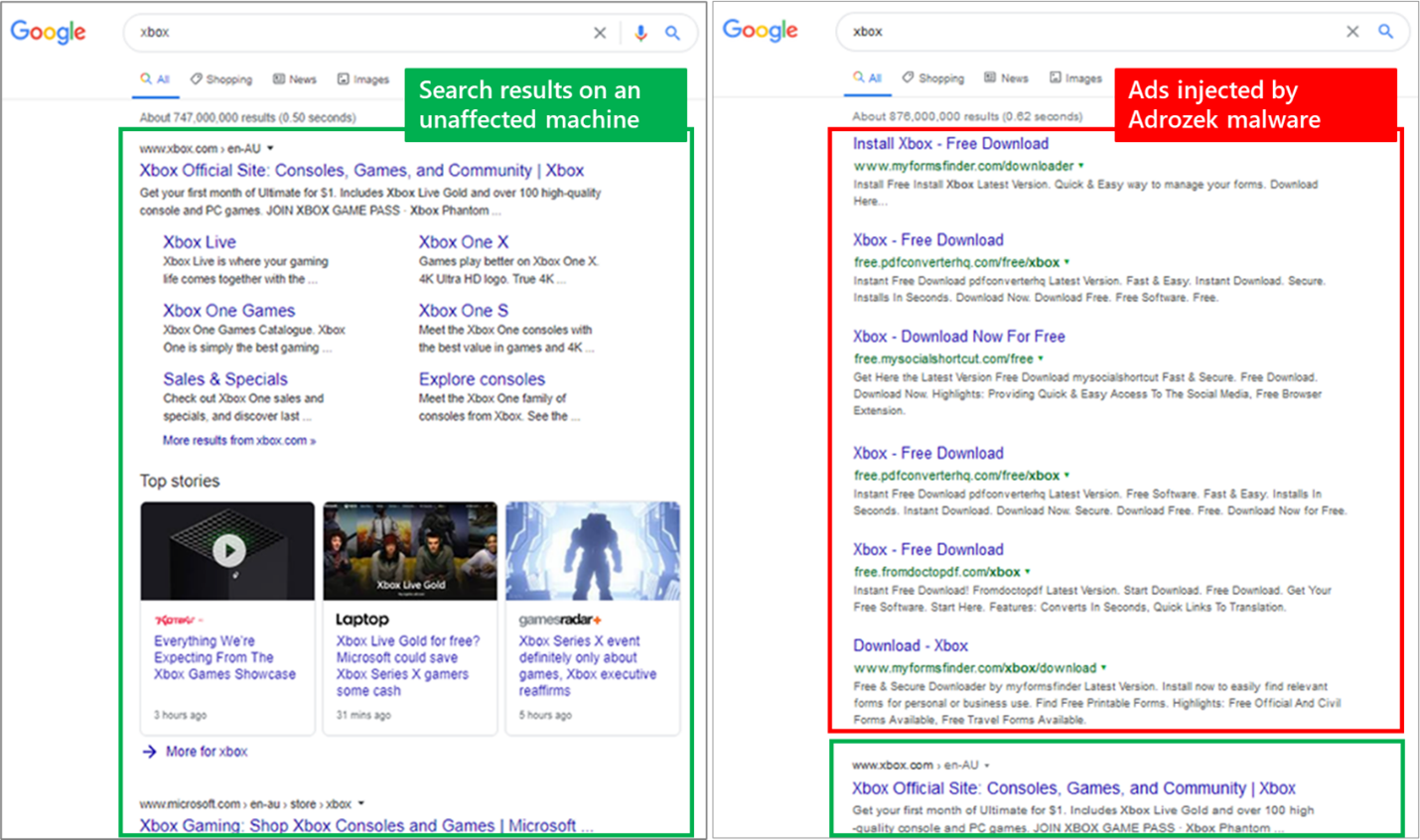
The Microsoft 365 Defender Research Team went public with this blog post on Thursday. At least since May 2020, a persistent malware campaign is underway, actively spreading an evolved browser modifier malware on a large scale. At its peak in August, the threat was observed on infecting over 30,000 devices daily. The malware is designed to insert ads into search engine results pages (see figure at right).
The malware threatens several browsers – Microsoft Edge, Google Chrome, Yandex Browser and Mozilla Firefox. The attackers try to reach as many Internet users as possible. Microsoft calls this family of browser modifiers Adrozek.
If the malware is able to infect a system, Adrozek adds browser extensions, modifies a specific DLL per target browser and changes browser settings. The goal is to insert additional, unauthorized ads into websites, often in addition to legitimate ads from search engines. The intended effect is that users searching for certain keywords accidentally click on these ads inserted by the malware, which lead to the linked pages. The attackers earn through affiliate advertising programs that pay according to the amount of traffic that is redirected to sponsored, affiliated pages.
Such a wide-ranging campaign requires the attackers to have an extensive, dynamic infrastructure. Microsoft's security researchers tracked 159 unique domains, each hosting an average of 17,300 unique URLs, which in turn hosted an average of more than 15,300 unique, polymorphic malware samples.
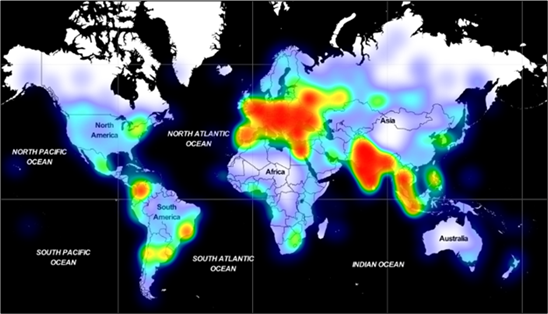
( Adrozek-Verteilung Souce: Microsoft)
In total, Microsoft's security researchers recorded hundreds of thousands of 'hits' of the Adrozek malware worldwide in the period from May to September 2020. There is a strong concentration in Europe as well as in South and Southeast Asia. As this campaign is still ongoing, this infrastructure will certainly continue to expand.
What happens during an infection?
The malware installer drops an .exe file with a random file name in the %temp% folder. This file installs the main payload in the Program Files folder and uses a file name that makes it appear to be legitimate audio software.
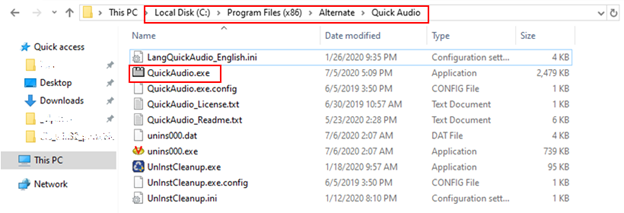
(Adrozek files, Source: Microsoft)
Although the malware uses different names, such as Audiolava.exe, QuickAudio.exe and converter.exe. However, it is installed like an ordinary program that can be accessed via Settings>Apps & Features.
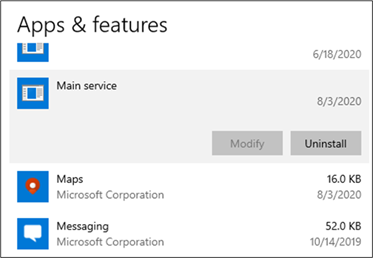
(Adrozek in Apps & features, Source: Microsoft)
There in Apps & features the malware can be uninstalled with the registered service. However, Adrozek adds a script to existing browser extensions. Although the malware targets different extensions in each browser, it adds the same malicious scripts to those extensions. In some cases, the malware changes the default extension by adding seven JavaScript files and a manifest.json file to the file path of the targeted extension. In other cases, it creates a new folder with the same malicious components.
In addition, the malware attempts to replace various browser DLLs and manipulate browser security settings. Microsoft's description of Adrozek shows that even browser hijackers that are not considered critical are becoming increasingly complex. While the main goal of the malware is to inject advertisements and link traffic to specific websites, the attack chain includes sophisticated behaviors. These are designed to allow the attackers to heavily embed the malware on the device. The addition of features to grab credentials shows that the cyber criminals can expand their targets to wreak further havoc.
Detect and remove Adrozek
According to Microsoft, Windows Defender (and thus probably other Microsoft products that use the same malware engine) detects the malware and blocks installation. End users who find this malware on their devices are advised by Microsoft to reinstall their browsers.
Considering the massive infrastructure that has been used to spread Adrozek, users should also be aware of how to avoid malware infections and the risks of downloading and installing software from untrusted sources and clicking ads or links on suspicious websites.
Users should also take advantage of URL filtering solutions, such as Microsoft Defender SmartScreen on Microsoft Edge. In addition, Microsoft recommends configuring security software to automatically download and install updates. In addition, running the latest versions of the operating system and applications and applying the latest security updates should help protect systems from such threats.
For enterprises, administrators should look to reduce the attack surface for these types of threats. This includes administrators enforcing the use of only authorized applications and services. Enterprise-class browsers such as Microsoft Edge offer additional security features such as conditional access and Application Guard that defend against threats in the browser. For more details, see the Microsoft post. (via)