 [German]I'm posting here an observation from readers that relates to Microsoft's Azure and Microsoft 365 services. Since mid-April 2024, there have been cyclical accesses to various domains that list "collector" as a subdomain. Virustotal probably has no complaints, so it's not a security issue. It is now clear to me what exactly is causing these accesses.
[German]I'm posting here an observation from readers that relates to Microsoft's Azure and Microsoft 365 services. Since mid-April 2024, there have been cyclical accesses to various domains that list "collector" as a subdomain. Virustotal probably has no complaints, so it's not a security issue. It is now clear to me what exactly is causing these accesses.
Reader observations on accesses
Blog reader Hapo22 has already reported on April 24, 2024 in the discussion area of the blog and shared his observation. Since Friday, April 19, 2024, he has observed many access attempts at the company proxies originating from local applications at the following addresses:
collector.azure.eaglex.ic.gov
collector.azure.microsoft.scloud
The reader said that both servers do not exist. The reader suspected that a debugging extension had been installed in Microsoft 365 apps and asked whether any of the readers could confirm these accesses in their network. On April 28, 2024, reader SwissMaik then explicitly confirmed these accesses.
I have just come across these two DNS requests on my Adguard Home. I'll have to look into it, but I've blocked the requests to be on the safe side.
Blog reader Johannes then writes in another note that a client in his environment tries to log in to both domains every few minutes. The reader had the domain collector.azure.eaglex.ic.gov checked by VirusTotal. The .gov domain is located under CISA.gov.
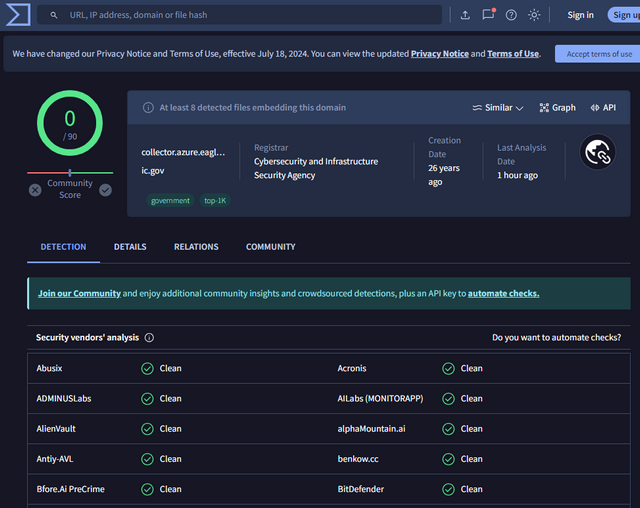
VirusTotal about collector.azure.eaglex.ic.gov
German blog reader Harry added later a comment, describing a few more details about what he found out:
We are also noticing more and more clients trying to resolve the two URLs mentioned.
If you go into the DNS client analysis (e.g. with DNSLookupView from NirSoft), you will find out that the process ms-teamsupdate.exe is responsible for these DNS requests when starting the new Teams Client 2.x.
Could be a bug or feature ;-)
Later he added in a comment, that in his environment only the Teams update process ms-teamsupdate.exe is responsible for the strange DNS requests on several clients. He used the DNSLookupView tool from NirSoft to see that ms-teamsupdate.exe attempts to resolve IPv4 and IPv6 at irregular intervals:
collector.azure.microsoft.scloud A
collector.azure.microsoft.scloud AAAA
collector.azure.eaglex.ic.gov A
collector.azure.eaglex.ic.gov AAAA
According to his DNS monitoring, one client produced more than 1000 queries in 30 minutes. That adds up to quite a lot of traffic.
Azure Machine Learning Data Collector
I then did some more research and finally came across an explanation for the whole thing. On April 18, 2024, Microsoft announced the general availability of the Azure Machine Learning Data Collector. The article Azure Machine Learning data collector is now generally available states that the Azure Machine Learning data collector enables real-time logging of input and output data from models deployed on managed online endpoints or Kubernetes online endpoints.
Azure Machine Learning stores the logged inference data in Azure Blob Storage. This data can then be used seamlessly for model monitoring, debugging or auditing, allowing you to monitor the performance of your deployment. More information on collecting data from models can be found in the article Data collection from models in production. And the two domains mentioned above also explain themselves. Microsoft operates an Azure for US authorities (Azure Government) as well as the public Azure cloud.




It's concerning to see unauthorized cloud access patterns involving collector.azure. This highlights the urgent need for improved security measures and monitoring. for more details, please visit