 [German]According to Microsoft, the partially not working ASLR memory protection in Windows 8, Windows 8.1 and Windows 10 is not a bug, but simply a feature that has been built in.
[German]According to Microsoft, the partially not working ASLR memory protection in Windows 8, Windows 8.1 and Windows 10 is not a bug, but simply a feature that has been built in.
A few days ago I had the issue within my blog post ASLR fails in Windows 8, 8.1 and 10 – but there is a fix. I wrote 'Developers have made a mistake that causes the ASLR mechanism not always work properly in Windows 8, Windows 8.1 and Windows 10.' Address Space Layout Randomization (ASLR) is a computer security technology designed to make it harder for attackers to exploit a buffer overflow.
CERT/CC vulnerability analyst Will Dormann discovered that ASLR did not randomly randomize the storage code locations of application binary files under certain conditions. While in Windows 7 and EMET the memory addresses of loaded modules were random by ASLR on restarting Windows, this was no longer the case in Windows 10. Dormann published his findings in a Tweet.
Microsoft disagrees with the analysis
Microsoft has rejected Will Dormann's analysis. The answer from Microsoft is that ASLR works as intended and that the lack of randomization that Will Dormann – with the support of Matt Miller from Microsoft – discovered, was a feature and not an error.
In short, ASLR works as intended and the configuration problem described by CERT/CC only affects applications where the EXE is not choosen ASLR. The configuration problem is not a vulnerability, does not cause additional risk and does not weaken the existing security situation of applications, says Microsoft. They posted the following table.
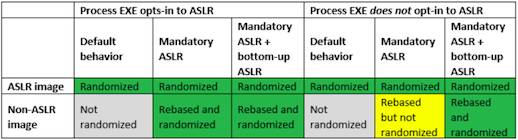
Microsoft ASLR table, Source: Microsoft
Microsoft said that Dormann's discovery only applied to the case that was colored yellow in the above table and added: "the entropy of images rebased by mandatory ASLR is inherently reliant on bottom-up randomisation being enabled for the process." All details may be found within Microsoft's blog post here. (via)



