 [German]During the last days I became aware of several security incidents and issues, which I would like to summarize in a short blog post. For example, the Android Messenger app allowed users to eavesdrop on each other. In addition, security researchers found an unsecured database with 100,000 data of Facebook users, which uncovered a huge credit card fraud and phishing campaign targeting Facebook users.
[German]During the last days I became aware of several security incidents and issues, which I would like to summarize in a short blog post. For example, the Android Messenger app allowed users to eavesdrop on each other. In addition, security researchers found an unsecured database with 100,000 data of Facebook users, which uncovered a huge credit card fraud and phishing campaign targeting Facebook users.
Vulnerability in Android Messenger app
Facebook is trying to bring the relevant app for direct messages to the user community on mobile devices. I myself use the desktop mode in the Chrome browser to save myself the Facebook app-trouble on Android devices. But the majority of users probably have Facebook Messenger installed as an app on Android.
In early October 2020, security researchers from Google's Project Zero discovered a security issue within the Android Messenger app. In Facebook Messenger, audio and video calls can be handled via the WebRTC API. To establish communication, a series of informal messages are exchanged between the calling and called device. Normally, the called party does not transmit audio until the user has agreed to accept the call.
However, there is a message type SdpUpdate that is not used to establish a connection. If a message of this type is sent to the called party's device while it is ringing, it causes the audio transmission to begin immediately. This could allow an attacker to monitor the called party's environment. This vulnerability has now been fixed by an update of the Android Messenger app.
Facebook credit card fraud uncovered through data leak
Security researchers at vpnMentor have discovered an open, unsecured database on the Internet that exposes a potentially massive phishing and credit card fraud operation targeting Facebook users. The unsecured database contained the private data of 100,000 of its victims stored by the fraudsters.
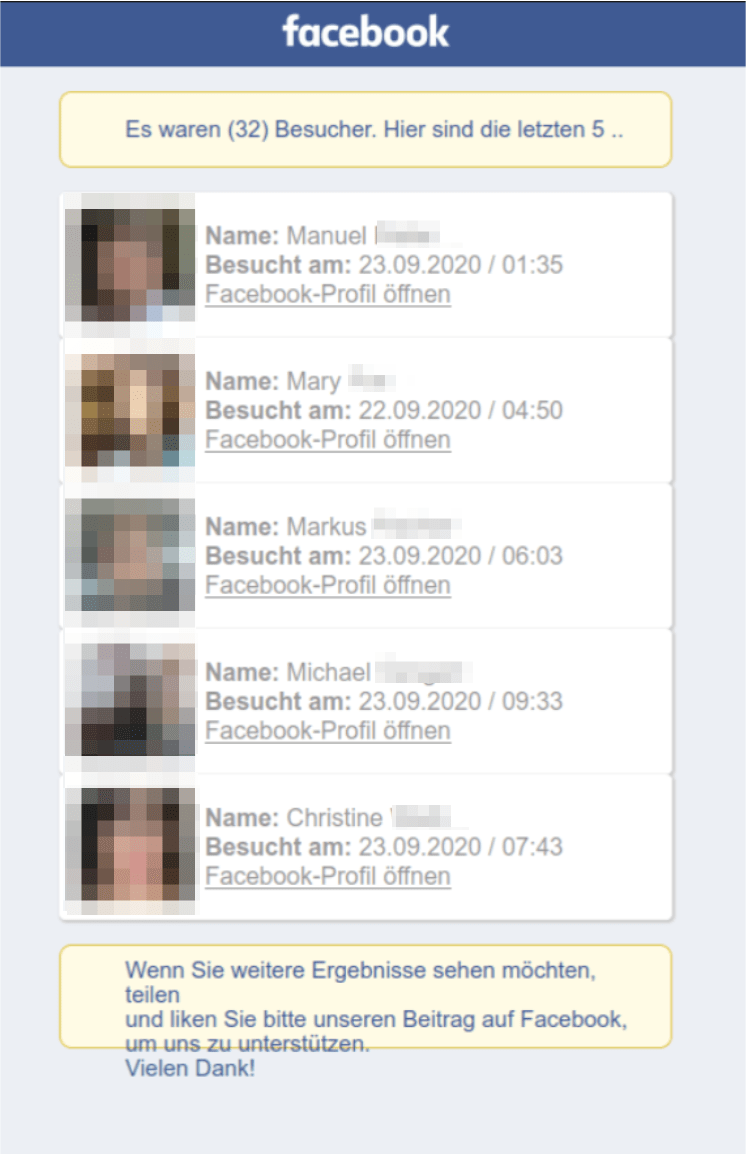
Facebook visitor list, source: vpnMentor
The scammers deceived Facebook users using a tool that pretended to reveal the visitors to their profiles. The tool required the victims to provide login information for their private accounts. The scammers used the stolen credentials to spread spam comments in Facebook postings through the victims' hacked account and to direct people to their network of scam sites. These websites eventually all led to a fake Bitcoin trading platform that was used to trick people into depositing at least 250 Euros and to scam the deposit amount. The operation targeted Facebook users worldwide. Details about this case can be read in this blog post by vpnMentor.



