![]() [German]In my blog post Windows 7 SP1: ESU Support for 2021 – Part 1 I had pointed out that from January 2021 a new ESU license is required to receive further security updates for this operating system. Those who do not have an ESU license (e.g. private users) or do not get it (e.g. because of Windows 7 Home or Windows Server 2008/R2) can use alternative solutions, which I present in part 2.
[German]In my blog post Windows 7 SP1: ESU Support for 2021 – Part 1 I had pointed out that from January 2021 a new ESU license is required to receive further security updates for this operating system. Those who do not have an ESU license (e.g. private users) or do not get it (e.g. because of Windows 7 Home or Windows Server 2008/R2) can use alternative solutions, which I present in part 2.
Some background
On 1/14/2020, Windows 7 SP1 (and Windows Server 2008/R2) reached the long announced end of support – there will be no more security updates by default. However, Microsoft will continue to provide security updates for companies until January 2023. To get these security updates on systems with Windows 7 SP1 or Windows Server 2008/R2, an ESU license from Microsoft is required (see Wow! Windows 7 get extended support until January 2023).
Problem #1: No ESU license for Windows 7 Home
However, with the approach Microsoft mentioned, which I covered in the article Windows 7 SP1: ESU Support for 2021 – Part 1, there is the problem that this ESU license for Windows 7 only applies to Professional and Enterprise/Ultimate. Owners of a Windows 7 SP1 Home are left out. In addition, private users will not necessarily want to buy an ESU license for over 100 euros/dollars.
Problem #2: No ESU license for Windows Server 2008/R2
The ESU license keys issued for Windows 7 SP1 cannot be used for Windows Server 2008/R2. The vendor Software Express mentioned in part 1 had made efforts to obtain ESU licenses for Windows Server 2008/R2 as well. Microsoft allows the purchase of the ESU key only via a Microsoft Enterprise Agreement (EA) or a Microsoft Business and Services Agreement (MBSA). This leaves people who still need to run Windows Server 2008 R2, but do not have access to such a licensing program, out in the cold. Therefore I recommend the following alternative from ACROS Security.
ACROS Security 0patch as an alternative
The alternative, especially for people who could not get an ESU license for Windows Server 2008/R2, are the micropatches from 0patch. ACROS Security provides the 0patch Pro license for 23,00 Euro (net) per client and year. This includes micropatches for the most important vulnerabilities.
(Source: ACROS Security)
Mitja Kolsek, the founder of ACROS Security, with whom I am in direct contact via Twitter, published the blog post 2021 2021 New Year's Resolution: "We Will Spend Less Time and Money on Security Patches" on the topic in mid-December 2020.
I had described the approach in the blog post Windows 7: Securing with the 0patch solution – Part 2. I myself use this solution on a client – and in 2020 there were numerous micropatches for vulnerabilities. So this works and is (as far as I know) the only solution to automatically patch a server 2008/R2 without ESU license (I don't see ByPassESU as a solution in the professional environment).
For private users there is even a free variant of the 0patch approach, which however does not receive all micropatches. I had described the different 0patch models in the blog post Project: Windows 7/Server 2008/R2 Life Extension & 0patch one month trial.
Note: The 0patch solution does not provide updates in the sense of Microsoft. The 0patch agent loads micropatches after booting Windows, which simply mitigates the known vulnerabilities. If the 0patch agent is uninstalled, the micropatches are also removed and the vulnerabilities are back. Nevertheless, the 0patch approach is a cheap and viable solution in my eyes.
ByPassESU for hobbyists
Furthermore, resourceful hobbyists have developed a solution called ByPassESU to install security updates for Windows 7 even without an ESU license. Some hints can be found in the post Windows 7 Sept. 2020 Updates: BypassESU v8 required. However, I don't see this approach as a solution I would use in corporate environments.
In December 2020, BypassESU v11 has been released (see the post Windows 7 ESU Bypass v10 ist erschienen [Update: ESU Bypass v11) on German site deskmodder.de, which will probably still work in 2021 – or will be updated to work in 2021. The use is legal in my estimation in a private environment, but I do not link sources. Who is interested in the topic, I refer to the colleagues of deskmodder.de, who provide details and a download link for the relevant files in this blog post.
Article series:
Windows 7 SP1: ESU Support for 2021 – Part 1
Windows 7 SP1/Server 2008/R2: Extended Support 2021 – Part 2
Similar articles
Wow! Windows 7 get extended support until January 2023
Windows 7 Extended Security Updates buyable from April 2019
Microsoft offers Windows 7 Extended Update Support to SMBs
Prices for Windows 7 Extended Security Updates till 2023
Windows 7: Free Extended Update Support and usage
Windows 7: Office 365 ProPlus Updates till 2023
Windows 7 Extended Security Updates (ESU) requirements
Windows 7 Extended Security Update (ESU) program available
Windows 7 Extended Security Updates (ESU) program, price and source for SMEs
Windows 7: Buy and manage ESU licenses – Part 1
Windows 7: Preparing for ESU and license activation – Part 2
Windows 7: ESU Activation inEnterprise Environment – Part 3
Windows 7: ESU questions and more answers – Part 4
Windows 7: Forcing February 2020 Security Updates – Part 1
Windows 7: Securing with the 0patch solution – Part 2
Windows 7/Server 2008/R2: 0patch delivers security patches after support ends
Project: Windows 7/Server 2008/R2 Life Extension & 0patch one month trial
0patch: Fix for Internet Explorer 0-day vulnerability CVE-2020-0674
0patch: Fix for Windows Installer flaw CVE-2020-0683
0patch fix for Windows GDI+ vulnerability CVE-2020-0881
0-day vulnerability in Windows Adobe Type Library
0patch fixes CVE-2020-0687 in Windows 7/Server 2008 R2
0patch fixes CVE-2020-1048 in Windows 7/Server 2008 R2
0patch fixes CVE-2020-1015 in Windows 7/Server 2008 R2
0patch for 0-day RCE vulnerability in Zoom for Windows
Windows Server 2008 R2: 0patch fixes SIGRed vulnerability
0patch fixes CVE-2020-1113 in Windows 7/Server 2008 R2
0patch fixes CVE-2020-1337 in Windows 7/Server 2008 R2
0patch fixes CVE-2020-1530 in Windows 7/Server 2008 R2
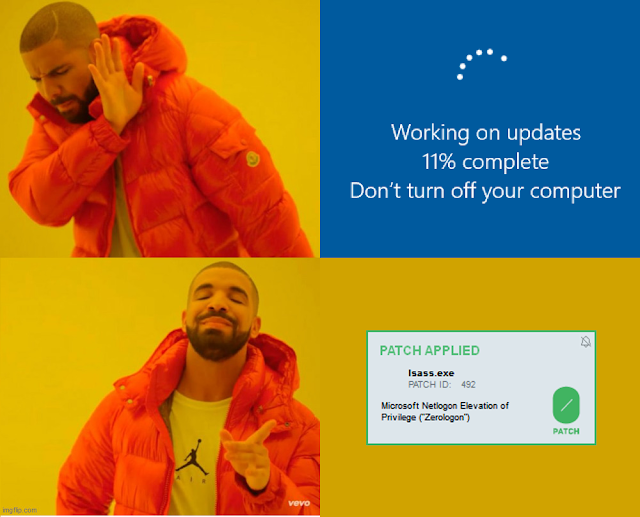
0patch fixes Zerologon (CVE-2020-1472) vulnerability in Windows Server 2008 R2
0patch fixes CVE-2020-1062 in Windows 7/Server 2008 R2
0patch supports Office 2010 with micro patches after the end of support (EOL)
Windows 7/Server 2008/R2 ESU support for the second year
Windows 7 ESU-Update KB4538483 (May 2020)
Windows 7 ESU Preparation Package Update KB4575903 (July 31, 2020)
Windows 7 Sept. 2020 Updates: BypassESU v8 required



