[German]A news for Windows users, encrypting their disks with Bitlocker. A YouTuber demonstrates how a vulnerability in "external" TPM chips can be exploited to determine a Bitlocker key within seconds. All you need is a Bitlocker key sniffer in the form of a Raspberry Pi Pico for around 10 US dollar.
[German]A news for Windows users, encrypting their disks with Bitlocker. A YouTuber demonstrates how a vulnerability in "external" TPM chips can be exploited to determine a Bitlocker key within seconds. All you need is a Bitlocker key sniffer in the form of a Raspberry Pi Pico for around 10 US dollar.
Notes on Bitlocker
Bitlocker is the feature provided by Microsoft in Windows for encrypting data carriers. The encryption solution is integrated in both Windows 10 and Windows 11 (as well as in earlier Windows versions) – and may also be activated on Home systems (see Windows 10/11 Home Edition and the OEM Bitlocker pitfall).
Bitlocker key extracted from TPM
The topic came to my attention this morning via a private message on Facebook (thanks for that) and the following post on Mastodon.
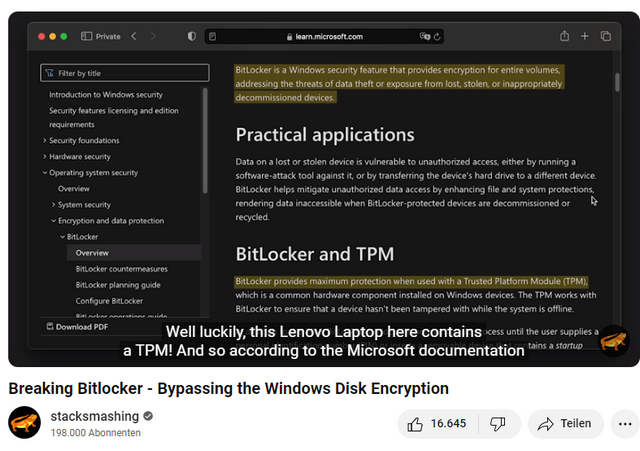
YouTuber stacksmashing has tackled the topic of Bitlocker and demonstrates a hardware attack to bypass the TPM-based Bitlocker encryption in the following video. According to him, this is exactly the scenario used on most Microsoft Windows devices.
The YouTuber writes that the PIN can also be activated via manage-bde, and not just via group policies. The whole thing should also work on TPM 2.0 in certain constellations, as described in this article from 2019.
This approach is not brand new, but has already been demonstrated (see Windows Bitlocker-Verschlüsselung trotz TPM ausgehebelt). And we recently had the WinRE story with the Bitlocker Security Feature Bypass vulnerability CVE-2024-20666, which is to be fixed via an update (see Microsoft is working on a fix for the installation error 0x80070643 (WinRE update KB5034441)), which also reveals a vulnerability in certain constellations. The attack also does not work with fTPM, where TPM is implemented in the CPU.
TomsHardware has taken a closer look at the YouTuber's approach and presented it in this article. YouTuber stacksmashing uses a Raspberry Pi Pico worth less than 10 euros to extract the required recovery key from the TPM module. This exploits a design flaw that occurs in many systems with a special Trusted Platform Module (TPM).
The background to this is that Bitlocker relies on an external TPM for some configurations in order to store critical information such as the platform configuration registers and the volume master key (some CPUs have this built in). With external TPMs, the TPM key is exchanged with the CPU via an LPC bus. The key is required to decrypt the data on the Bitlocker drive.
The Raspberry Pi Pico, which acts as a TPM sniffer, takes advantage of the fact that communication between the CPU and the external TPM on the LPC bus is tracked unencrypted during booting. This allows an attacker to intercept critical data on the way between the two units and thus determine the Bitlocker encryption keys. The video shows the YouTuber unscrewing a notebook, connecting the TPM sniffer and then displaying the Bitlocker key. This takes less than 43 seconds – although unscrewing the notebook counts as part of this time.