[German]I'm pulling it out separately in a blog post after several blog readers pointed it out to me. The March 2024 security update from March 12, 2024 for Windows Server causes a memory leak in LSASS (for all Windows Server variants), which then leads to performance problems on domain controllers (DC) after some time and may send them to digital nirvana. Here is some information on this issue. Addendum: The issue has been confirmed.
[German]I'm pulling it out separately in a blog post after several blog readers pointed it out to me. The March 2024 security update from March 12, 2024 for Windows Server causes a memory leak in LSASS (for all Windows Server variants), which then leads to performance problems on domain controllers (DC) after some time and may send them to digital nirvana. Here is some information on this issue. Addendum: The issue has been confirmed.
First reader hint
German blog reader riedenthied posted a comment on March 19, 2024 here and reported a massive problem on domain controllers after installing the March 2024 security update. He wroter:
There seems to be a memory leak in the lsass.exe, which sooner or later causes the domain controller to crash. […]
Seems to affect all server variants, from 2016 to 2022. The larger the environment, the faster it goes. I have not yet read a statement from Microsoft, but several users report that they have support tickets running with MS.
Uninstalling the March update probably helps, but I won't consider doing that on the domain controllers. I'd rather restart them every few days.
The reader mentioned that this bug was already addressed in my German blog post Exchange Server Sicherheits-Updates (12. März 2024) in this German comment by blog reader Dreise. I had seen this, but because it also occurred on Windows 11 clients, I had not yet addressed it separately and decided to continue monitoring it. Since March, 19m 2024, however, I have been receiving more reader messages pointing out this problem.
This bug in the form of an lsass memory leak already existed in November 2022, I had discussed it at the time in the blog post https://borncity.com/win/2022/11/25/windows-server-november-2022-updates-cause-lsass-memory-leak/.
Another reader hint
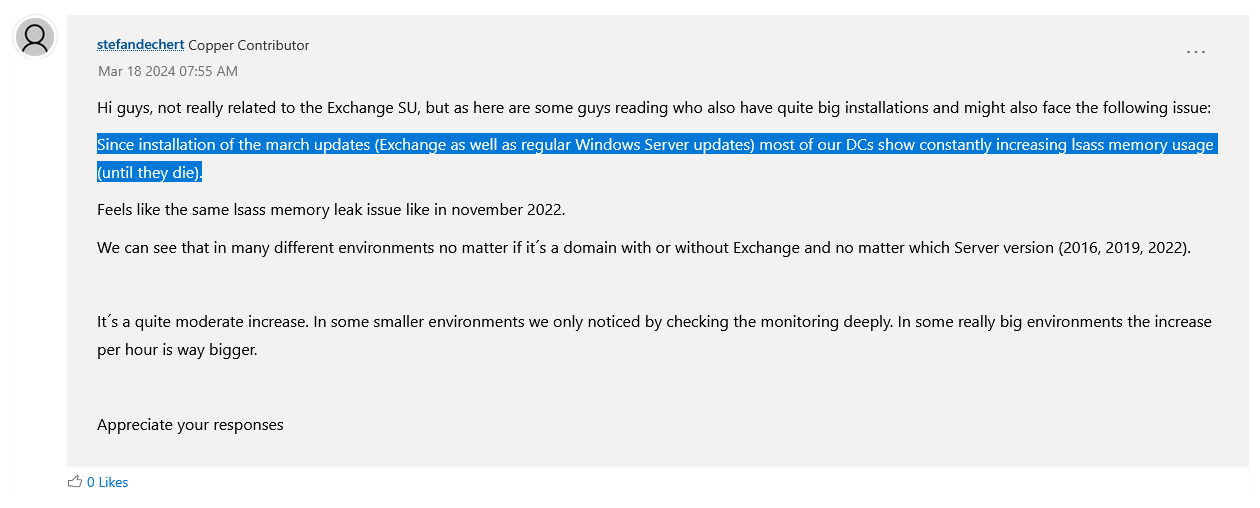
On March 19, 2024, Sebastian D. and Christopher G. also contacted me by email and reported the error. Sebastian pointed out that there was a mention in the Exchange Forum that the March 2024 updates of Windows on the DCs may lead to a steadily increasing memory consumption of Isass. He wrote:
In the Exchange Forum there is a finding that the March updates of Windows on the DCs may cause a steadily increasing memory consumption of lsass. Just search for Isass at the link. Doesn't have to be anything bad in the end. Others may also report the problems and it may only lead to a problem after time X.
Christopher described the whole thing in more detail in his email and provided evidence of the memory leak. Christopher wrote to me about this:
Hello Mr. Born,
Since the latest Windows updates, we have been experiencing considerable performance problems on the DCs. As I have already discovered other users in your blog (comment by German user Dreise) who have the same problem, I wanted to draw your attention to this. It may be of interest to you or you may even be able to contribute to a solution with your reach.
The reader wrote that you can also find similar reports about this problem in the Microsoft Tech Community (same link to the Exchange post as above). I have extracted the post below.
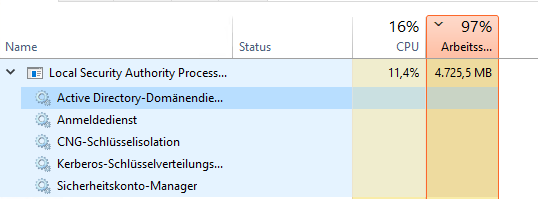
Christoph describes the problem as follows: Since our domain controllers (Windows Server 2019) installed the latest Windows updates (see image) at the weekend, they regularly run at >95% memory. The following screenshot shows this utilization:
In the reader's specific case, it is update KB5035849, but all Windows servers are probably affected as described above. Christoph wrote: "Permanently uninstalling the updates was not an option for us and so far we have also been able to solve it temporarily by restarting the system. "
After I've published the German edition of this blog post, I got mixed feedback. Some blog readers confirmed the observation, while others wrote, that everything seems fine with their domain controllers and Windows Server instances. It seems that Microsoft is investigating this issue, as I've read in the Techcommunity Exchange post within the comment section.
Microsoft has confirmed the issue
Addendum: Minutes after I published this blog article, I recognized, that Microsoft has confirmed this issue. Within the Know Issues section for Windows Server Microsoft has published the entry Issue with Kerberos requests on domain controllers may cause LSASS memory leaks.
Microsoft writes that after installing the March 12, 2024 security updates, a memory leak may occur in the Local Security Authority Subsystem Service (LSASS) on domain controllers (DCs). This occurs when local and cloud-based Active Directory domain controllers serve Kerberos authentication requests.
The memory leak can become so extreme that it causes LSASS to crash, triggering an unplanned reboot of the underlying domain controllers (DCs). According to Microsoft, it only affects environments in organizations using some Windows Server platforms with the following Windows variants.
- Windows Server 2022
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012 R2
Microsoft says that the cause has now been identified. The developers are working on a solution that will be published in the next few days. Microsoft will then update the linked support article. Until this solution is found, the only option is to uninstall the March 2024 update in question (a bad idea, as some vulnerabilities have been closed) or to monitor the memory utilization of the servers and reboot them from time to time if necessary.
Addendum: Microsoft has released first out-of-band-updates (OOB) with fixes, see Windows Server: Fix for (Kerberos) LSASS memory leak through March 2024 updates.
Similar articles:
Microsoft Security Update Summary (March 12, 2024)
Patchday: Windows 10-Updates (March 12, 2024)
Patchday: Windows 11/Server 2022-Updates (March 12, 2024)
Windows Server 2012 / R2 and Windows 7 (March 12, 2024)
Windows 10/Server 2019: Update KB5035849 fails with error 0xd0000034