 [German]Microsoft has just released an analysis of the Nodersok infection chain. The malware runs entirely in memory and is difficult for antivirus programs such as Defender to detect (but Microsoft Defender ATP can detect the malware). There are thousands of infections of Windows systems, including in Europe.
[German]Microsoft has just released an analysis of the Nodersok infection chain. The malware runs entirely in memory and is difficult for antivirus programs such as Defender to detect (but Microsoft Defender ATP can detect the malware). There are thousands of infections of Windows systems, including in Europe.
The Nodersok malware
There is malware which is named Nodersok at Microsoft (Talos calls it Divergent), which is files-less, but is rolled out via Node.js in the form of encrypted scripts. The entire malicious code is unpacked in memory and then executed. Therefore, a virus scanner like Microsoft Defender cannot detect this malware. The following tweet deals with the whole thing.
Every step of #Nodersok's infection chain runs only legitimate executables. All relevant functionalities reside in scripts and shellcodes that come in encrypted and are decrypted and run while only in memory. More in our analysis of this #fileless threat: https://t.co/d4XC5dQeg7
— Microsoft Security Intelligence (@MsftSecIntel) September 27, 2019
According to this Microsoft post the new malware campaign, called Nodersok, uses its own LOLBins image – and it uses two very unusual, legitimate tools for infected computers:
- Node.exe, the Windows implementation of the popular Node.js framework that is used by countless web applications.
- WinDivert, a powerful network packet capture and editing program.
A LOLBins stands for Living off the land Binary and is a term for a binary file that an attacker uses to perform actions that go beyond the original purpose (see the explanations here).
As with any LOLBin, these tools are not themselves malicious or vulnerable; they provide important functionality for legitimate use under Windows. But the Nodersok uses the tools for its own purposes. It is not uncommon for attackers to download legitimate third-party tools to infected computers (e.g. PsExec is often misused to execute other tools or commands).
Difficult to detect
But Nodersok uses a long chain of file-less techniques to install some very special tools. The ultimate goal is to turn infected computers into zombie proxies. Due to the file-less approach, the attack is very difficult to detect (Microsoft Defender does not detect the malware because there are no files to scan) – but the attack's behavior creates a visible 'footprint' that is clearly visible to anyone who knows where to look. With its set of advanced defense technologies, Microsoft Defender ATP is able to detect the threat throughout the infection chain.
Thousands of machines infected
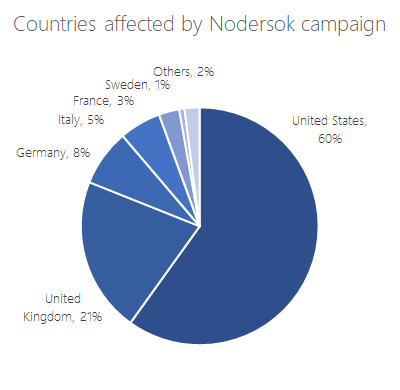
The Nodersok campaign has attacked thousands of machines in recent weeks, with most targets in the United States and Europe. The majority of the systems attacked are in the hands of consumers. But about 3% of the attacked Windows machines are operated in organizations in areas such as education, professional services, healthcare, finance and retail.
 (Source: Microsoft)
(Source: Microsoft)
The Microsoft diagram above shows that about 8% of the attacks detected on Windows systems in Germany are in Germany. Microsoft discovered this malware campaign ready in mid-July 2019 when suspicious patterns appeared in the abnormal use of MSHTA.exe from Microsoft Defender ATP telemetry. In the days that followed, further anomalies became apparent, leading to a tenfold increase in activity. The campaign peaked at the end of August and the beginning of September 2019 before fading away. Further details can be found in the Microsoft article here or in this article on The Hacker News.




Yes, Nodersok campaign has attacked many more machines even my friend's machine also affected through this infection. Its the time to more awareness to prevent such infection.