[German]AnyDesk confirmed a few hours ago that the cyber incident took place "at the end of December 2023". In addition, the old certificate of "philandro Software GmbH" is now likely to be criticized. The background to this is that a third party had applied to DigiCert for a "revoke" and this application was granted. Here is an updated overview of what has happened in the last 24 hours.
[German]AnyDesk confirmed a few hours ago that the cyber incident took place "at the end of December 2023". In addition, the old certificate of "philandro Software GmbH" is now likely to be criticized. The background to this is that a third party had applied to DigiCert for a "revoke" and this application was granted. Here is an updated overview of what has happened in the last 24 hours.
AnyDesk GmbH's information policy on the cyber incident that took place, only releasing details step-by-step when it can no longer be denied, seems to really annoy some people, as I can see from some of the emails sent to me. In my series of articles (see end of post), I followed the topic from the suspicion of a hack in January 2023 (see AnyDesk: Be careful in using that remote support software) to the confirmation of the attack (see AnyDesk confirmed, they have been hacked in January 2024, Production systems affected – Part 1) and in the aftermath. This makes it easy to follow the state of information here on the blog, what the Federal Office for Information Security (BSI) communicated and what the affected company disclosed and when. Looking back, many of the suspicions I expressed here in the blog were confirmed. Now there are new developments.
Confirmation of the attack in December 2023
I had already pointed out in the article AnyDesk hack – more details (FAQ from Feb. 5, 2024) – Part 8 that I have information or evidence that the cyber incident at AnyDesk did not occur "in mid-January 2024", as stated in the first edition of the FAQ on the "Incident".
AnyDesk has now updated its FAQ on February 7, 2024 and writes that, following an investigation, the incident began "in late December 2023". The relevant addition reads (thanks to the reader for pointing this out):
Diligent forensic investigation revealed that the incident had started in late December 2023.
So it confirms what I already indicated on February 6, 2024 based on reader information and the CERT-FR document in the blog post AnyDesk hack – more details (FAQ from Feb. 5, 2024) – Part 8 and already noted in my blog post AnyDesk hack already noticed on December 20, 2023? – Part 9 in more detail.
In addition, there is now a note (see also this German comment) in the FAQ about which customers were affected by the incident: "Affected customers were limited to users based in continental Europe, with the exception of Spain and Portugal." Whether this is sufficiently precise for customers is up to them to decide.
Old certificate recalled
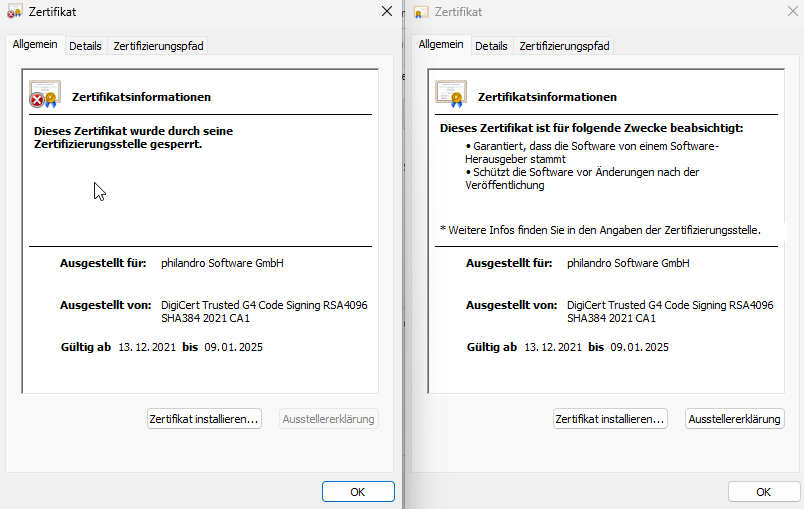
And there is another new development: Users of AnyDesk clients signed with the old "philandro Software GmbH" certificate should now have warnings or errors. Michael writes in this comment:
Apparently MS has now classified all philandro certificates as potentially malicious due to an update for SmartScreen, which now also affects all those with custom clients who are still stuck with 7.0.14 as there is still no 7.0.15 available. This will make the custom clients unusable/uninstallable.
The old certificate of "philandro Software GmbH" has been recalled. The managing director of a company I know contacted me a few minutes ago and wrote that he had asked DigiCert to revoke the old certificate of "philandro Software GmbH". I have the correspondence with DigiCert – they have checked the process since February 6, 2024 and confirmed the revocation of the certificate on February 7, 2024 (message is from 5:37 pm).

Anyone who calls up the certificate check should then receive the above display with the status "revoked". Can this already be confirmed? I don't have any old versions and no time to test this. But someone wrote on Mastodon that the new clients show the certificate as "revoked", but the old clients report a valid certificate from "philandro Software GmbH" (see following screenshot).
Anyone still working with Customs clients that are digitally signed with the old certificate should therefore urgently update the client. In my German blog posts there is this comment and this comment with hints (thanks to the readers) on how the client 8.0.x could be forced for custom builds.
Articles:
AnyDesk confirmed, they have been hacked in January 2024, Production systems affected – Part 1
AnyDesk hack undercover – more information and thoughts – Part 2
AnyDesk hack undercover – Suspicious cases and more – Part 3
AnyDesk hack undercover – Access data offered for sale – Part 4
AnyDesk hack – A review – Part 5
AnyDesk hack – Review of the German CERT BSI report – Part 6
AnyDesk hack – Notes on exchanging certificates for Customs clients 7.x – Part 7
AnyDesk hack – more details (FAQ from Feb. 5, 2024) – Part 8
AnyDesk hack already noticed on December 20, 2023? – Part 9
AnyDesk hack confirmed as of December 2023; old certificate recalled – Part 10
AnyDesk hack: Revoke chaos with old certificates? – Part 11
AnyDesk hack: Newly signed clients available; what are your experiences? – Part 12
Similar article:
Störung bei AnyDesk, jemand betroffen?
AnyDesk: Be careful in using that remote support software
Kritische Schwachstelle (CVE-2023-22518) in Atlassian Confluence-Servern
Atlassian verstärkt Warnung vor Ausnutzung der Confluence-Schwachstelle CVE-2023-22518