There are several critical vulnerabilities in Microsoft Defender, that put Windows systems at risk. A security researcher has published an 0-day-exploit named BlueHammer on April 3, 2026, that has been patched on April 14, 2026. But there is still an unpatched vulnerability, where the security researcher has published the RedSun exploit. And ther is UnDefend, allowing to stop Windows Defender.
There are several critical vulnerabilities in Microsoft Defender, that put Windows systems at risk. A security researcher has published an 0-day-exploit named BlueHammer on April 3, 2026, that has been patched on April 14, 2026. But there is still an unpatched vulnerability, where the security researcher has published the RedSun exploit. And ther is UnDefend, allowing to stop Windows Defender.
Controversy Over the MSRC Team's Incompetence
A security researcher with the alias Chaotic Eclipse constantly publishes zero-day exploits on GitHub, affecting Microsoft Defender shipped in Windows. The reason for each action is – in my opionion – to outline the internal working methods of the Microsoft Security Response Team (MSRT). The team members have become so conditioned to processing security reports strictly by the book that security reports are often misclassified or incorrectly assessed.
The BlueHammer exploit
Some time ago, Chaotic Eclipse reported a vulnerability in the MSRT that affected Defender's behavior. As I understand it, he received a negative response. In response, Chaotic Eclipse made the information about the vulnerability public on X on April 3, 2026, and posted a proof of concept (PoC) for an exploit on GitHub.
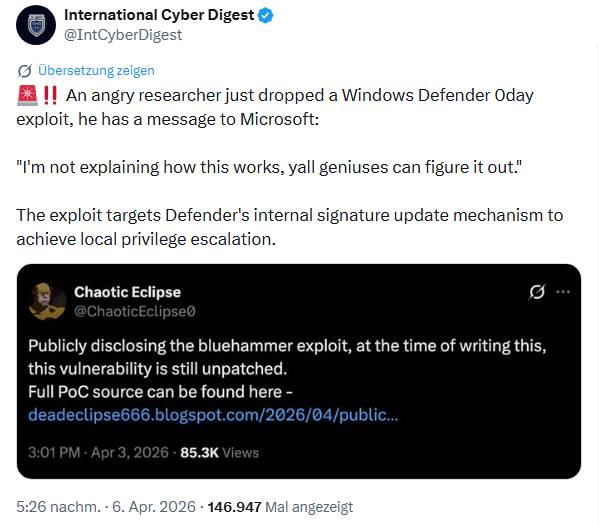
The tweet above addresses the issue I described in my German blog post BlueHammer: Windows 0-day-Schwachstelle [use the build-in translator of the blog, to change the language].On April 14, 2026, Microsoft released a patch—and I addressed this in a follow-up post titled BlueHammer-Nachlese: Defender-Patch vom 14.4.2026 und Analyse von Fortra which also included an analysis by Fortra.
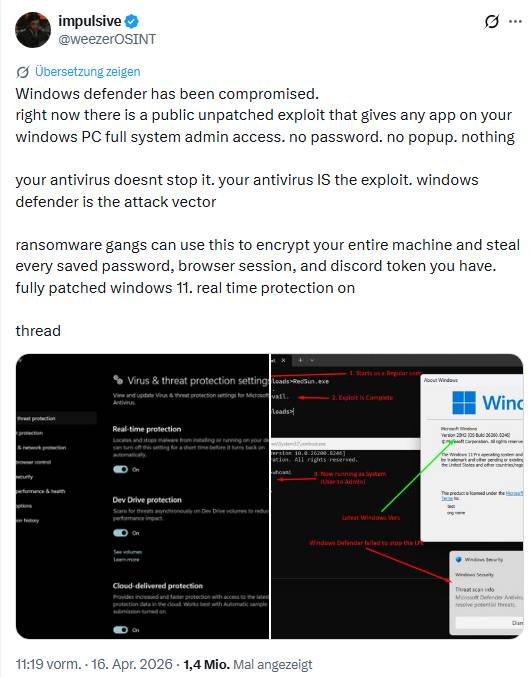
RedSun: Another Windows Defender 0-day
I came across information about another, as yet unpatched, vulnerability in Windows Defender via the tweet below. The post warns that the Defender included with Windows has been "compromised."
It says, there is a publicly known, unpatched exploit that grants any app on a Windows system full system administrator privileges. The attack vector is Microsoft Defender. Ransomware gangs could exploit this to encrypt the entire system and steal all stored passwords, browser sessions, and Discord tokens. This is reportedly possible even on a fully patched Windows 11 system with real-time protection enabled.
The zero-day exploit exploits a race condition: If Microsoft Defender detects a suspicious file marked with a cloud tag, it attempts to "repair" it. This repair involves Defender copying the file back to its original location.
The exploit now uses the OPLOCK technique and a junction to redirect this write operation to C:\Windows\System32. While Defender "believes" it is saving the files to a temporary folder, they are actually written to the C:\Windows\System32 folder. This way, attackers could trick Defender into delivering an infected file containing a payload directly to the System32 folder itself. These files can then be executed with system privileges. Chaotic Eclipse has published the exploit on GitHub.
UnDefend blocks Defender Updates
In addition to the aforementioned 0-day exploits BlueHammer (CVE-2026-33825) and RedSun, Chaotic Eclipse has also released the tool UnDefend within the past 14 days. UnDefend is a repository published on GitHub containing a Windows Defender denial-of-service (DoS) tool. This tool can blog Defender signature updates – and in some condition it's able to stop Microsoft Defender operation complete. Details may be found at GitHub.